Multi-Factor Authentication (MFA) is a security mechanism that requires users to provide two or more independent factors of authentication to verify their identity. Instead of relying solely on…



PKCE (Proof Key for Code Exchange) is a security extension to OAuth 2.0 that protects the Authorization Code flow from interception attacks—especially for public clients like mobile apps,…

Risk-Based Authentication (RBA) is an adaptive security approach that evaluates the risk level of a login attempt and adjusts the authentication requirements accordingly. Instead of always requiring the…
Salted Challenge Response Authentication Mechanism (SCRAM) is a password-based authentication protocol standardized by the IETF (commonly used as a SASL mechanism).

SASL is a protocol-agnostic authentication layer defined so that an application protocol (like IMAP or LDAP) can “hook in” standardized auth exchanges without reinventing them.
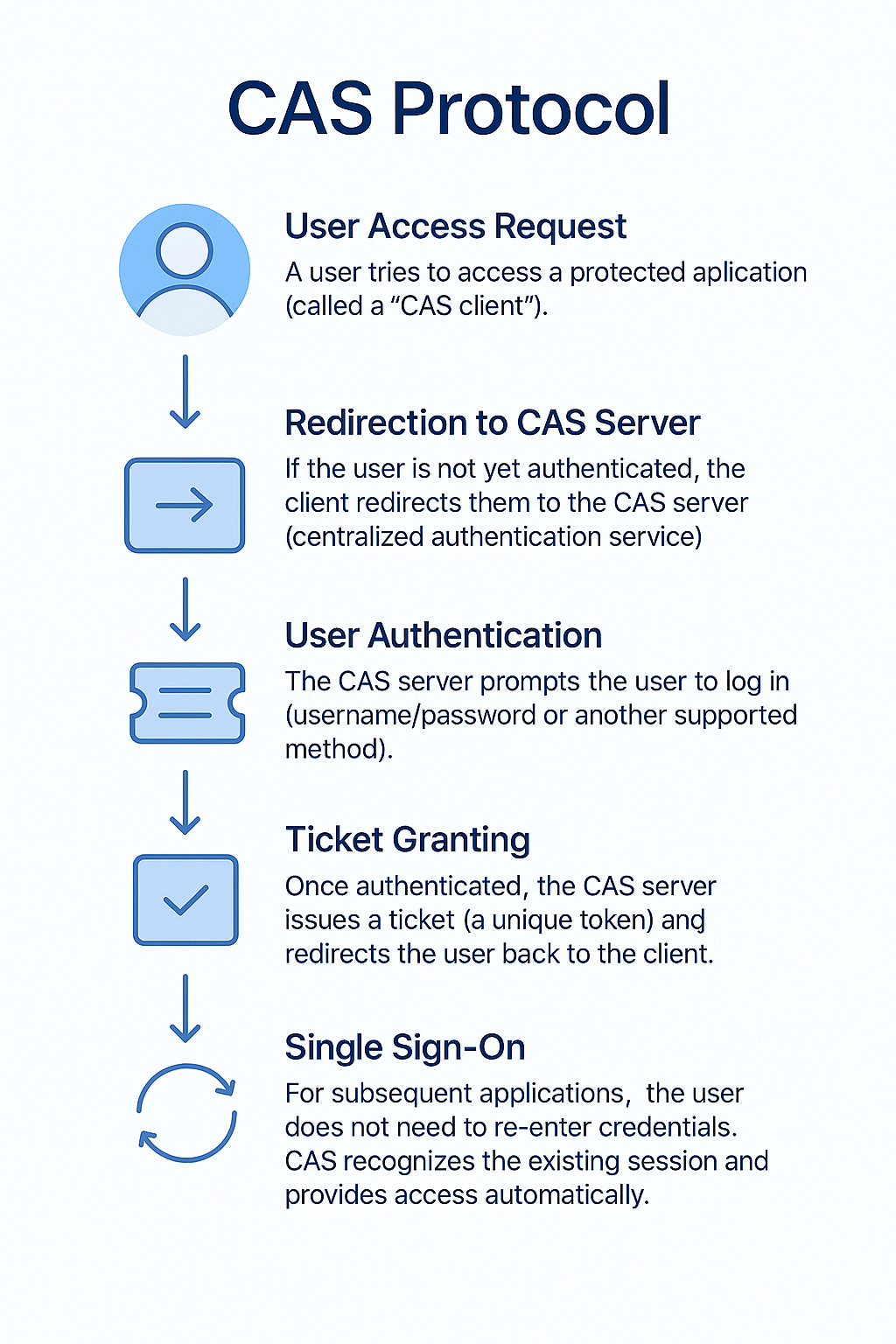
The Central Authentication Service (CAS) is an open-source, single sign-on (SSO) protocol that allows users to access multiple applications with just one set of login credentials. Instead of…