A CSPRNG is a type of algorithm that generates numbers that appear random but are actually produced by a deterministic process. Unlike regular pseudo-random number generators (PRNGs), which…

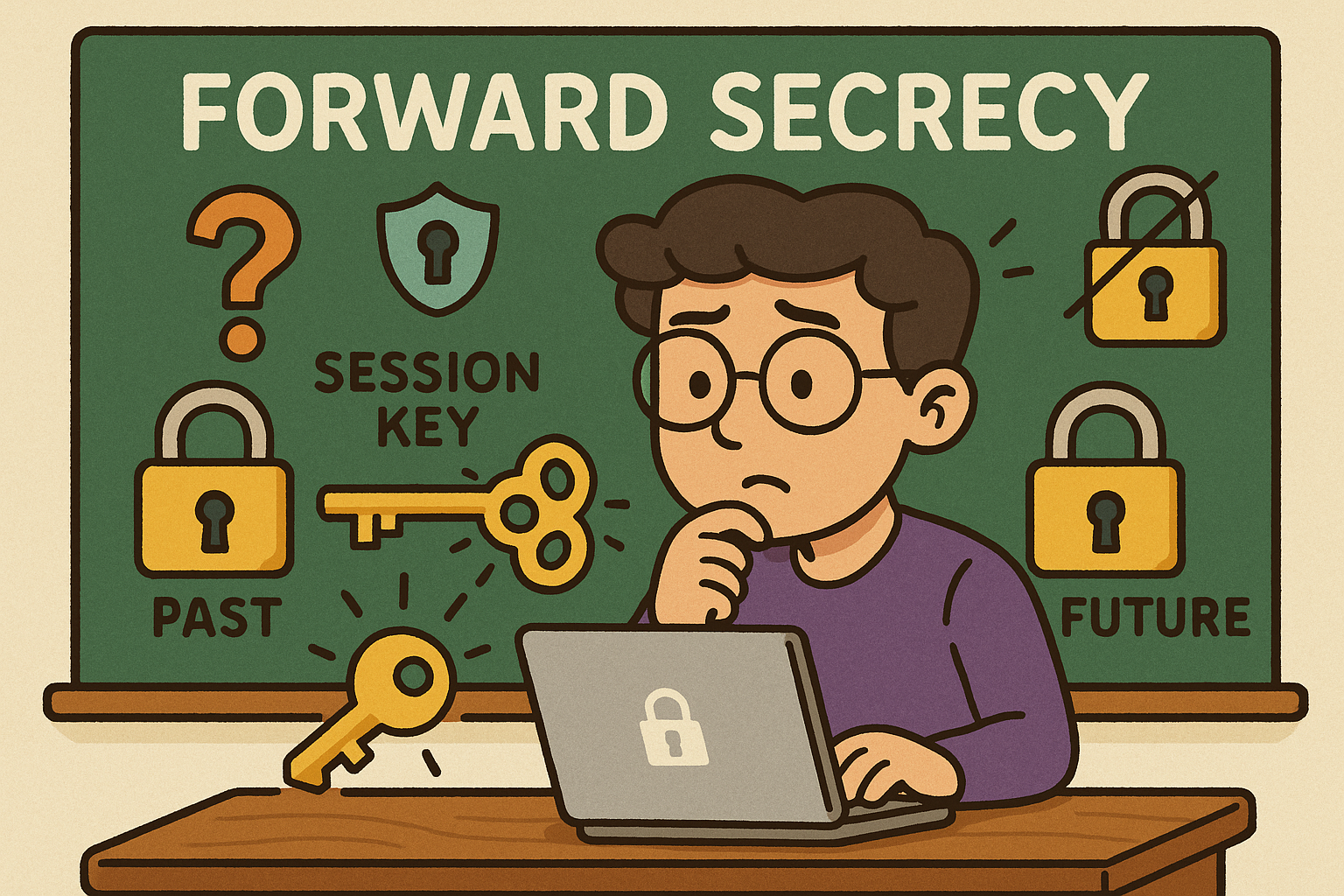
Forward Secrecy (also called Perfect Forward Secrecy or PFS) is a cryptographic property that ensures the confidentiality of past communications even if the long-term private keys of a…
Homomorphic Encryption (HE) is an advanced form of encryption that allows computations to be performed on encrypted data without ever decrypting it. The result of the computation, once…
OCSP is an IETF standard that lets clients (browsers, apps, services) check whether an X.509 TLS certificate is valid, revoked, or unknown—in real time—without downloading large Certificate Revocation…

A Deterministic Random Bit Generator (DRBG) is an algorithm that generates a sequence of random-looking bits from a given initial value called a seed. Unlike true random number…

Secure Socket Layer (SSL) is a cryptographic protocol originally designed to secure communication over networks. Modern “SSL” in practice means TLS (Transport Layer Security)—the standardized, more secure successor…
CVE (Common Vulnerabilities and Exposures) is an international system that provides a standardized method of identifying and referencing publicly known cybersecurity vulnerabilities. Each vulnerability is assigned a unique…

Transport Layer Security (TLS) is a cryptographic protocol that ensures secure communication between computers over a network. It is the successor to Secure Sockets Layer (SSL) and is…

A Man-in-the-Middle (MITM) attack is when a third party secretly intercepts, reads, and possibly alters the communication between two parties who believe they are talking directly to each…
CAPTCHA, short for Completely Automated Public Turing test to tell Computers and Humans Apart, is one of the most common tools used to protect websites from bots and…