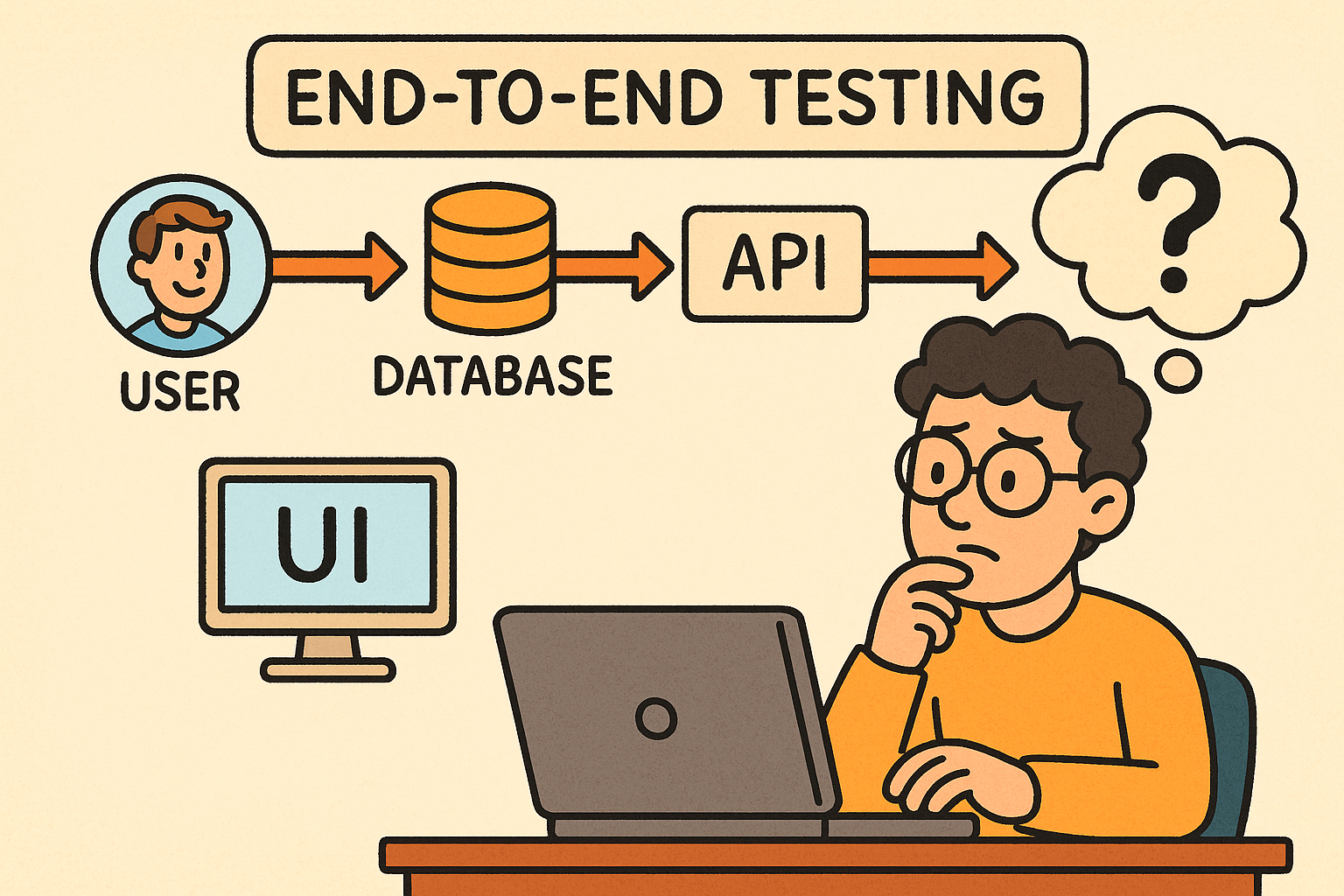
End-to-End (E2E) testing verifies an application’s workflow from start to finish, ensuring all components — from UI to database to external services — work seamlessly together. This post…
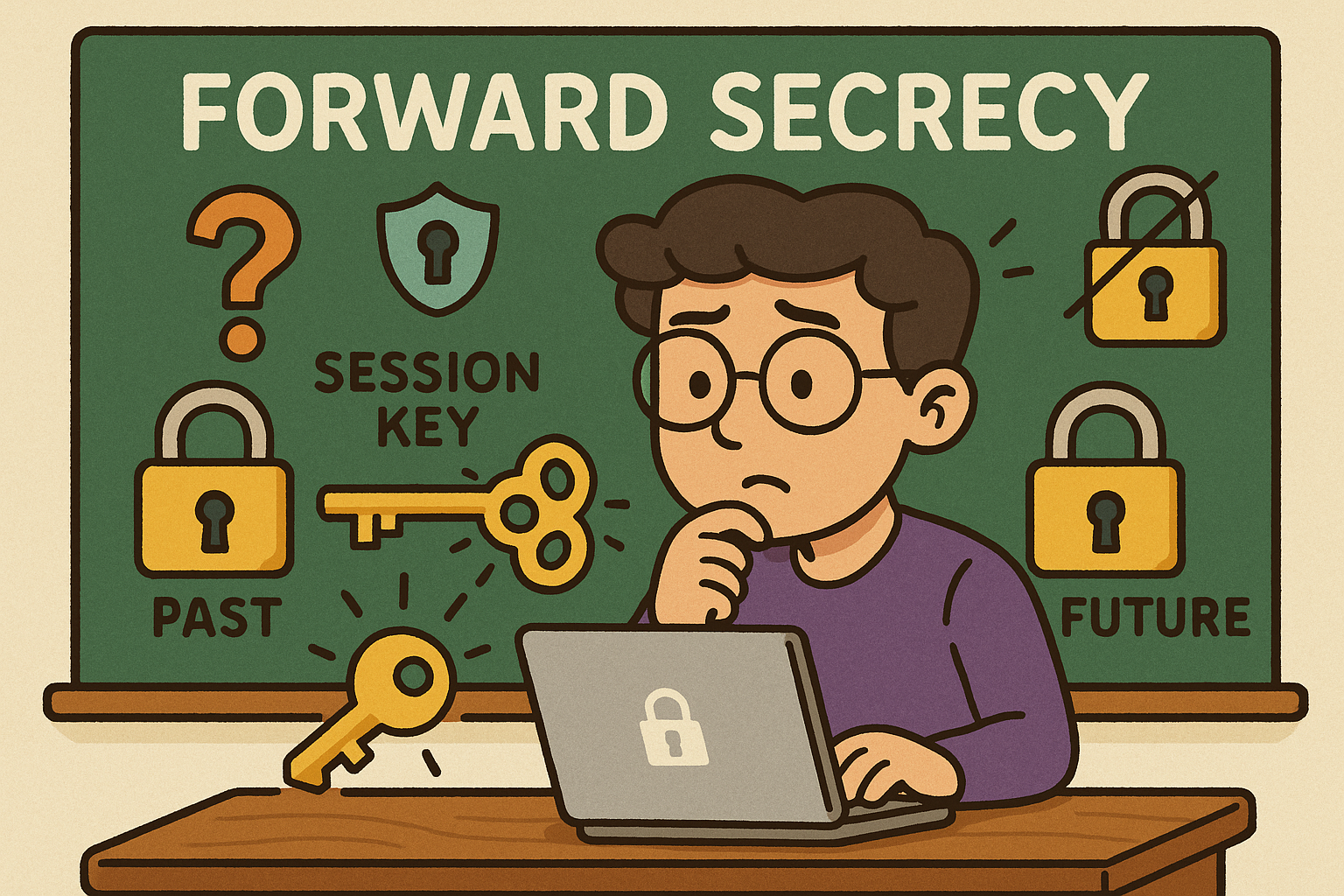
Forward Secrecy (also called Perfect Forward Secrecy or PFS) is a cryptographic property that ensures the confidentiality of past communications even if the long-term private keys of a…
OCSP is an IETF standard that lets clients (browsers, apps, services) check whether an X.509 TLS certificate is valid, revoked, or unknown—in real time—without downloading large Certificate Revocation…

Secure Socket Layer (SSL) is a cryptographic protocol originally designed to secure communication over networks. Modern “SSL” in practice means TLS (Transport Layer Security)—the standardized, more secure successor…

Transport Layer Security (TLS) is a cryptographic protocol that ensures secure communication between computers over a network. It is the successor to Secure Sockets Layer (SSL) and is…

A Man-in-the-Middle (MITM) attack is when a third party secretly intercepts, reads, and possibly alters the communication between two parties who believe they are talking directly to each…