A/B testing lets teams make product decisions with data, not hunches. This guide covers history, core components, how it works end-to-end, benefits, common pitfalls, when to use it,…

Acceptance Testing is a type of software testing conducted to determine whether a system meets business requirements and is ready for deployment. It is the final phase of…
AddressSanitizer (ASan) is a fast memory error detector built into modern compilers (Clang/LLVM and GCC). When you compile your C/C++ (and many C-compatible) programs with ASan, the compiler…

Aspect-Oriented Programming (AOP) is a programming paradigm that focuses on separating cross-cutting concerns from the main business logic of a program. In traditional programming approaches, such as Object-Oriented…

An AVL tree (named after Adelson-Velsky and Landis) is a self-balancing Binary Search Tree (BST). For every node, the balance factor (height of left subtree − height of…
Big-O notation describes how an algorithm’s running time or memory grows as the input size n gets large. It gives an upper bound on growth—e.g., “this algorithm runs…
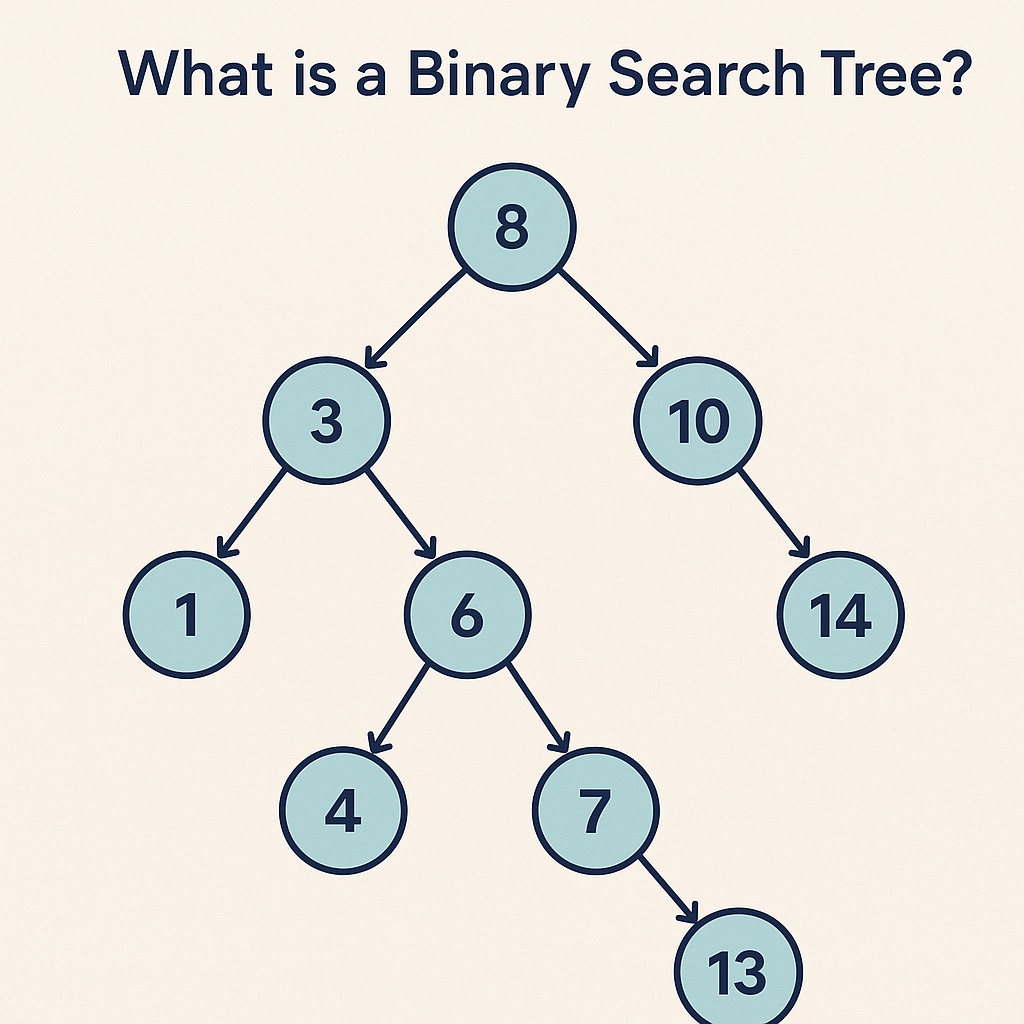
A Binary Search Tree (BST) stores keys in sorted order so you can search, insert, and delete efficiently—typically in O(log n) time—if the tree stays balanced. It’s great…
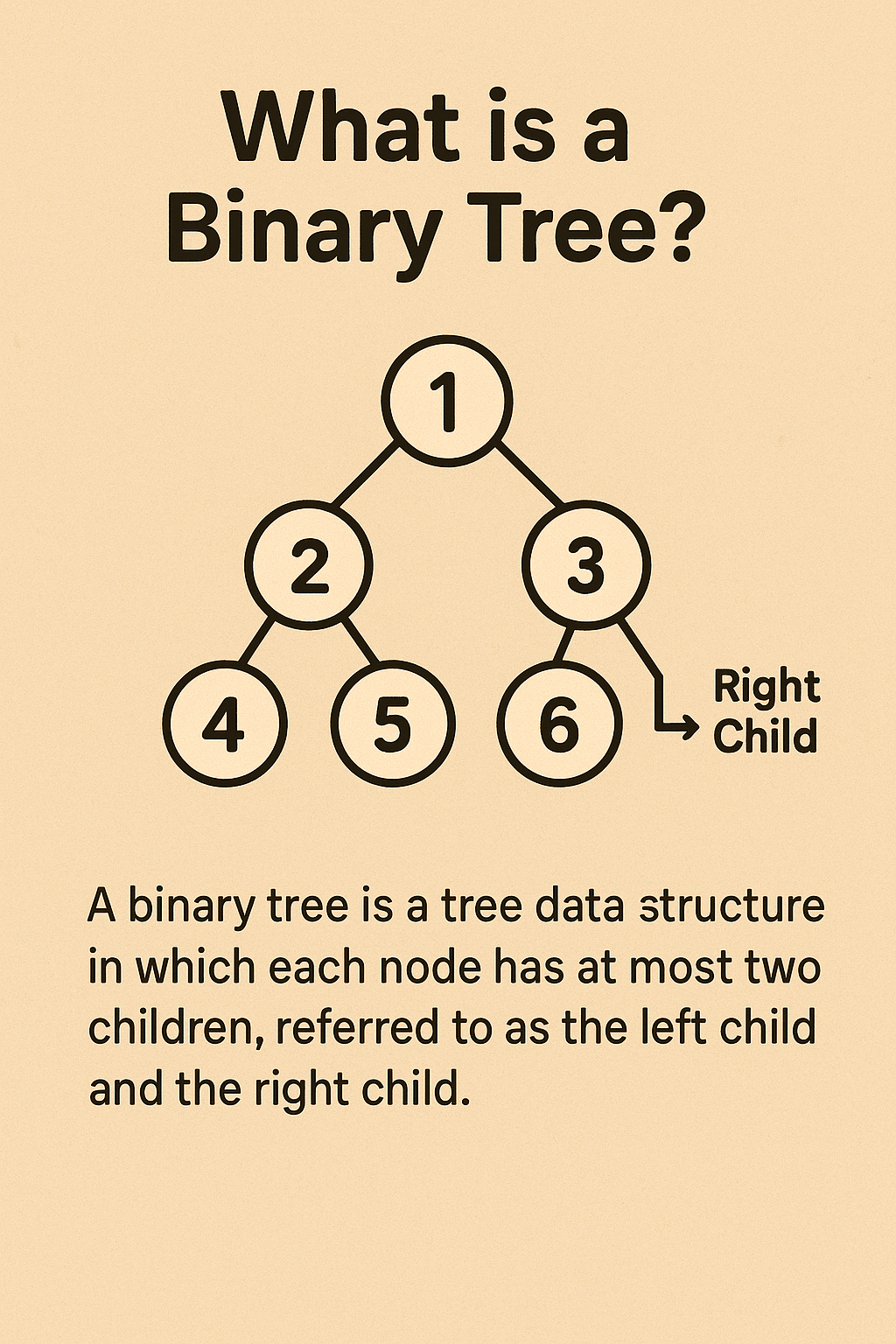
A binary tree is a hierarchical data structure where each node has at most two children. It’s great for ordered data, fast lookups/insertions (often near O(log n)), and…

Code katas are short, repeatable programming exercises designed to improve specific skills through deliberate practice. Borrowed from martial arts, the term “kata” refers to a structured routine you…

Code refactoring is the process of restructuring existing computer code without changing its external behavior. The main purpose is to improve the internal structure of the code—making it…
A code review is the process of systematically examining source code written by a developer to identify mistakes, improve quality, and ensure adherence to coding standards. It is…
Command Query Responsibility Segregation (CQRS) is a software architecture pattern that separates the responsibilities of reading data (queries) and writing data (commands) into two distinct models. Instead of…
A Conflict-free Replicated Data Type (CRDT) is a data structure that allows multiple computers or systems to update shared data independently and concurrently without requiring coordination. Even if…
Contact testing is a software testing approach where different components, services, or systems that “contact” each other are tested to ensure they communicate correctly. It focuses on the…

A CSPRNG is a type of algorithm that generates numbers that appear random but are actually produced by a deterministic process. Unlike regular pseudo-random number generators (PRNGs), which…
A Dead Letter Queue (DLQ) is a secondary queue linked to a primary “work” queue (or topic subscription). When a message repeatedly fails processing—or violates rules like TTL,…
Domain-Driven Development (DDD) is a software design approach introduced by Eric Evans in his book Domain-Driven Design: Tackling Complexity in the Heart of Software. At its core, DDD…
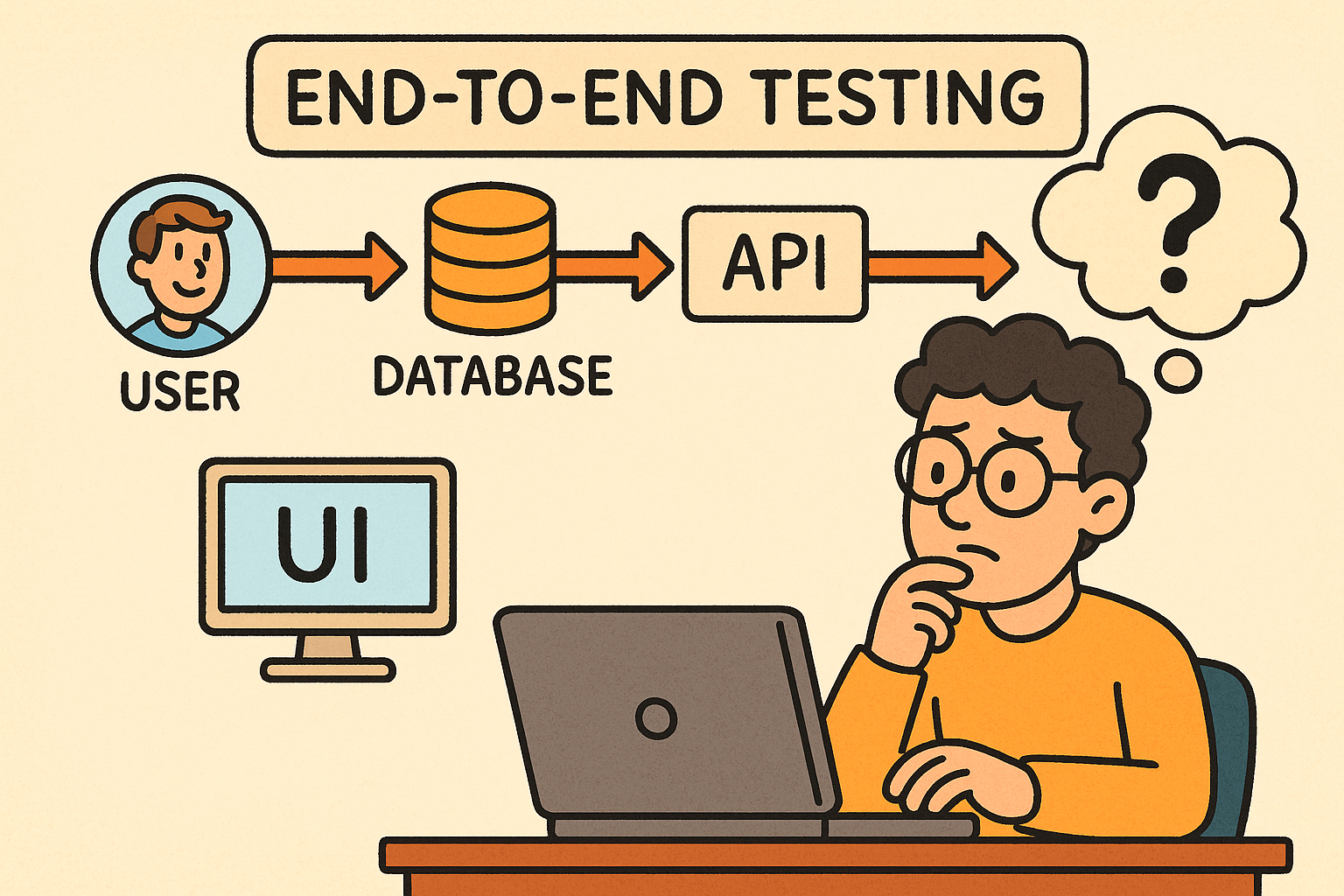
End-to-End (E2E) testing verifies an application’s workflow from start to finish, ensuring all components — from UI to database to external services — work seamlessly together. This post…
In computer science, not everything is built to last forever. Some concepts, processes, and resources are intentionally ephemeral—temporary by design, existing only for as long as they are…
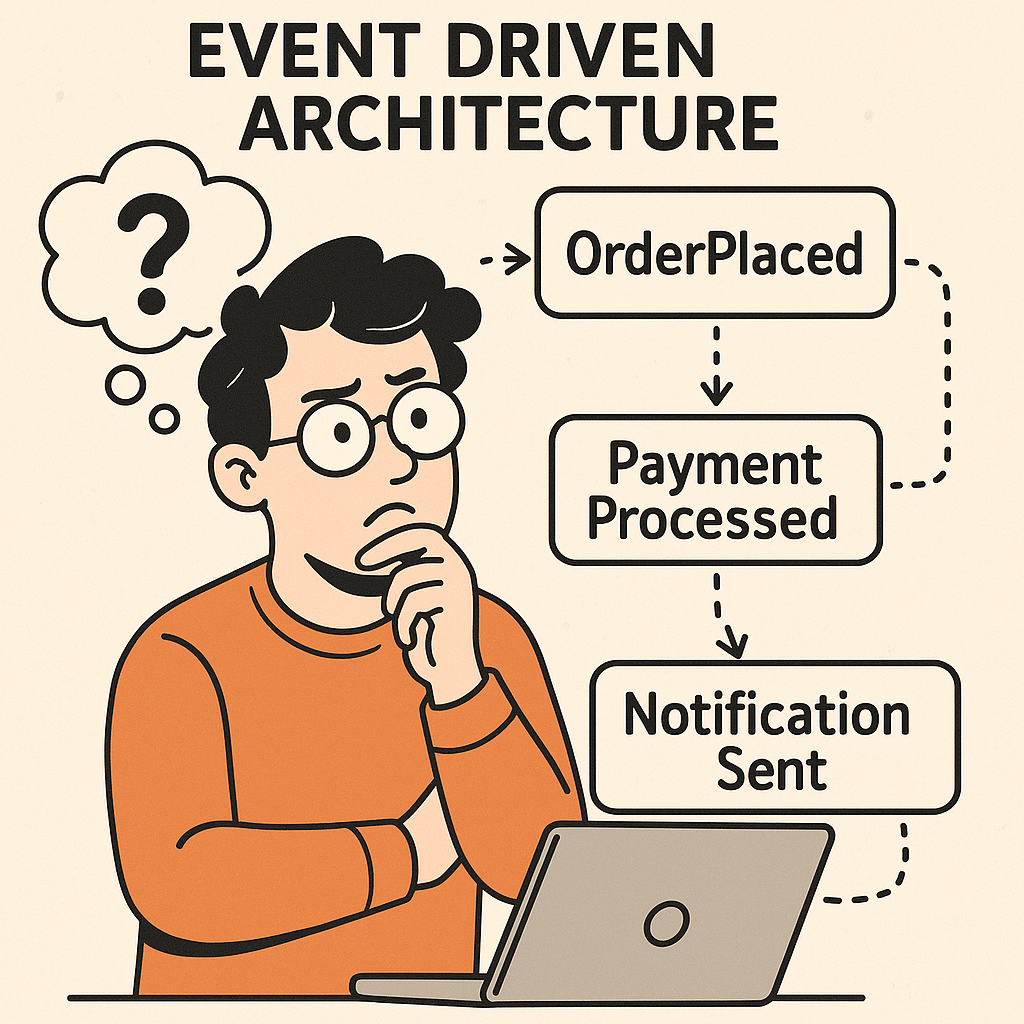
Event Driven Architecture (EDA) is a modern software design pattern where systems communicate through events rather than direct calls. Instead of services requesting and waiting for responses, they…
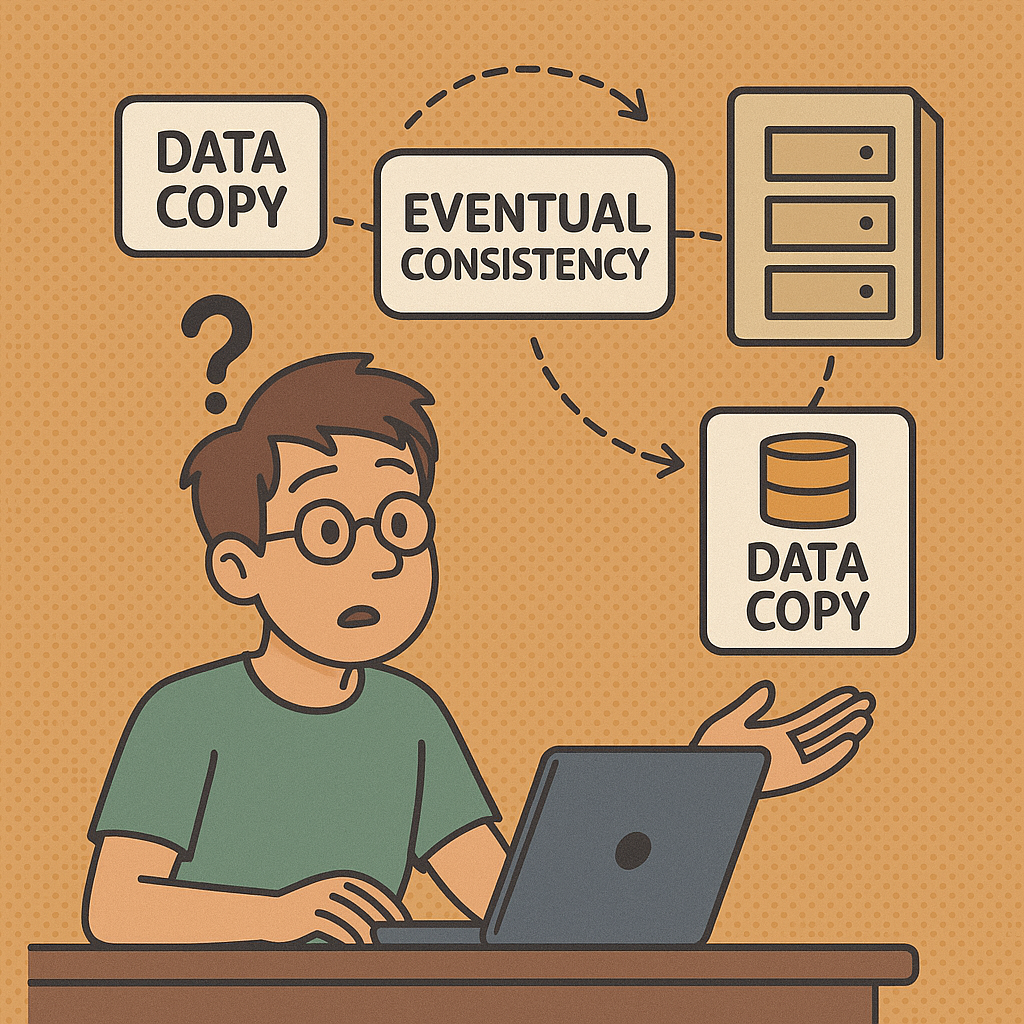
Eventual consistency is a consistency model used in distributed computing systems. It ensures that, given enough time without new updates, all copies of data across different nodes will…
Extreme Programming (XP) is an agile software development methodology that emphasizes customer satisfaction, flexibility, and high-quality code. It focuses on short development cycles, frequent releases, constant communication with…

Foreign Function Interfaces (FFIs) let code written in one language call functions or use data structures written in another. In practice, FFIs are the “bridges” that let high-level…
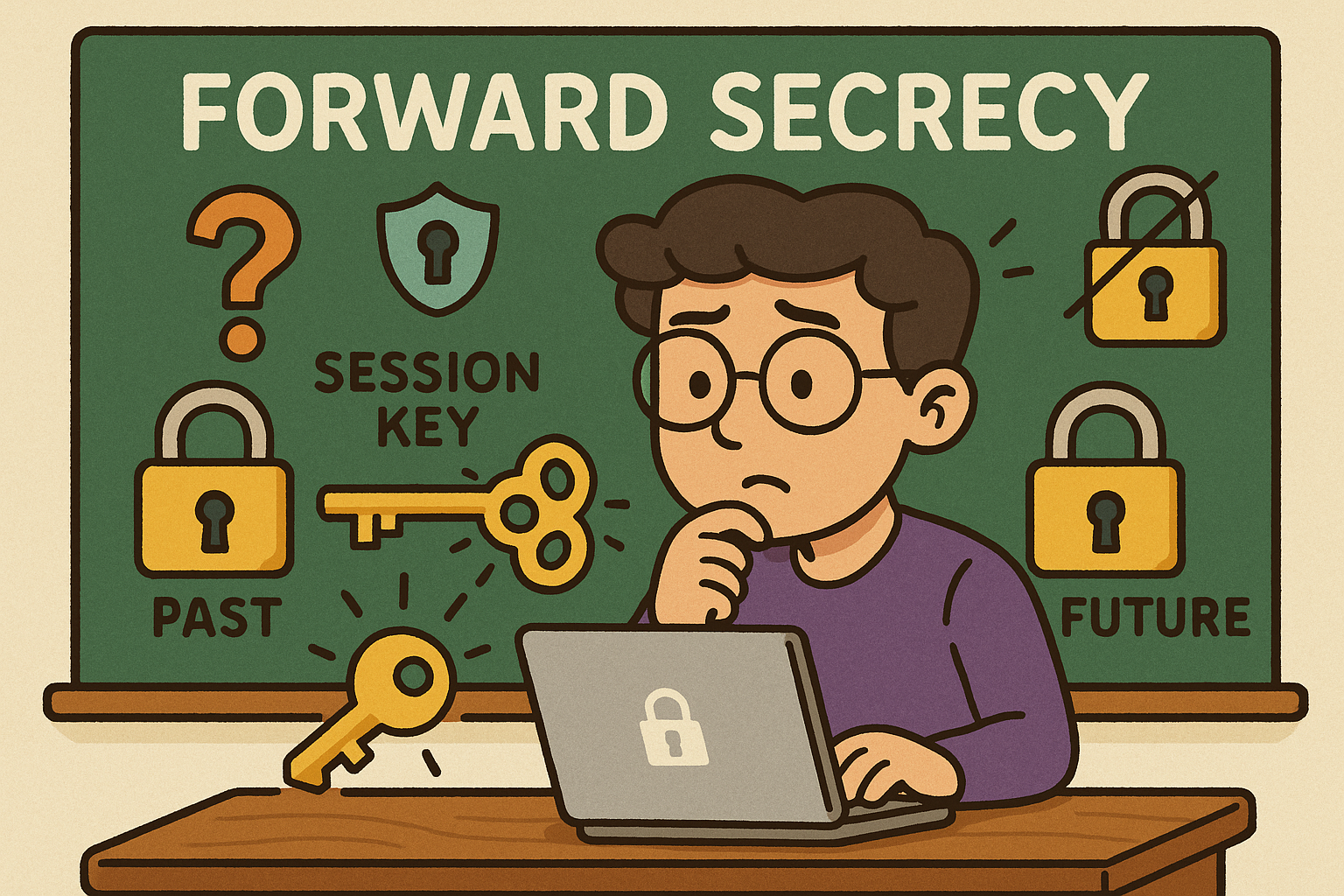
Forward Secrecy (also called Perfect Forward Secrecy or PFS) is a cryptographic property that ensures the confidentiality of past communications even if the long-term private keys of a…
Understanding the Frequentist approach in A/B testing is essential for making data-driven decisions with confidence. This statistical framework interprets probability as the long-run frequency of events, helping teams…

Fuzzing (or “fuzz testing”) is an automated technique for finding bugs by supplying a program with many inputs that are unusual, unexpected, or deliberately malformed, and observing for…
Homomorphic Encryption (HE) is an advanced form of encryption that allows computations to be performed on encrypted data without ever decrypting it. The result of the computation, once…

A practical, example-driven guide to implements vs extends in Java: what they mean, how they differ, when to use each, and how to fold good interface and inheritance…
Java was designed with primitives for performance and memory efficiency. Later, Java introduced generics, Collections, and object-oriented APIs that need reference types. Wrapper classes (like Integer) bridge primitives…
Integration testing verifies that multiple parts of your system work correctly together—modules, services, databases, queues, third-party APIs, configuration, and infrastructure glue. Where unit tests validate small pieces in…
Inversion of Control (IoC) is a design principle in software engineering that shifts the responsibility of controlling the flow of a program from the developer’s custom code to…
ISO/IEC/IEEE 42010 is an international standard that provides guidance for describing system and software architectures. It ensures that architecture descriptions are consistent, comprehensive, and understandable to all stakeholders.

The KISS principle stands for “Keep It Simple, Stupid”, a design philosophy that emphasizes simplicity in systems, software, and problem-solving. Originally coined in the 1960s by the U.S.…
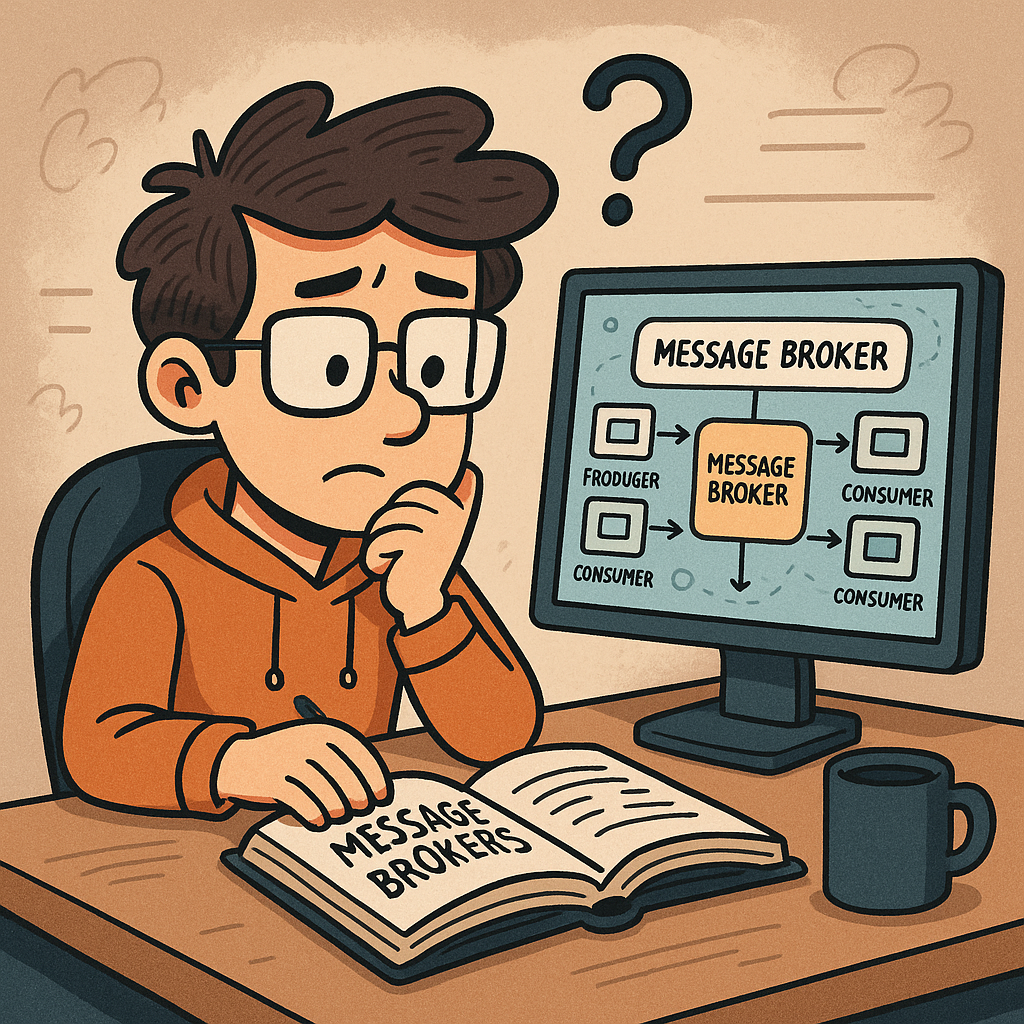
A message broker is middleware that routes, stores, and delivers messages between independent parts of a system (services, apps, devices). Instead of services calling each other directly, they…

Understanding the Minimum Detectable Effect (MDE) is essential for designing statistically valid A/B tests. MDE represents the smallest measurable difference between control and variant groups that an experiment…

A Minimum Viable Product (MVP) is the most basic version of a product that still delivers value to users. It is not a full-fledged product with every feature…

Multi-Factor Authentication (MFA) is a security mechanism that requires users to provide two or more independent factors of authentication to verify their identity. Instead of relying solely on…

OCSP is an IETF standard that lets clients (browsers, apps, services) check whether an X.509 TLS certificate is valid, revoked, or unknown—in real time—without downloading large Certificate Revocation…

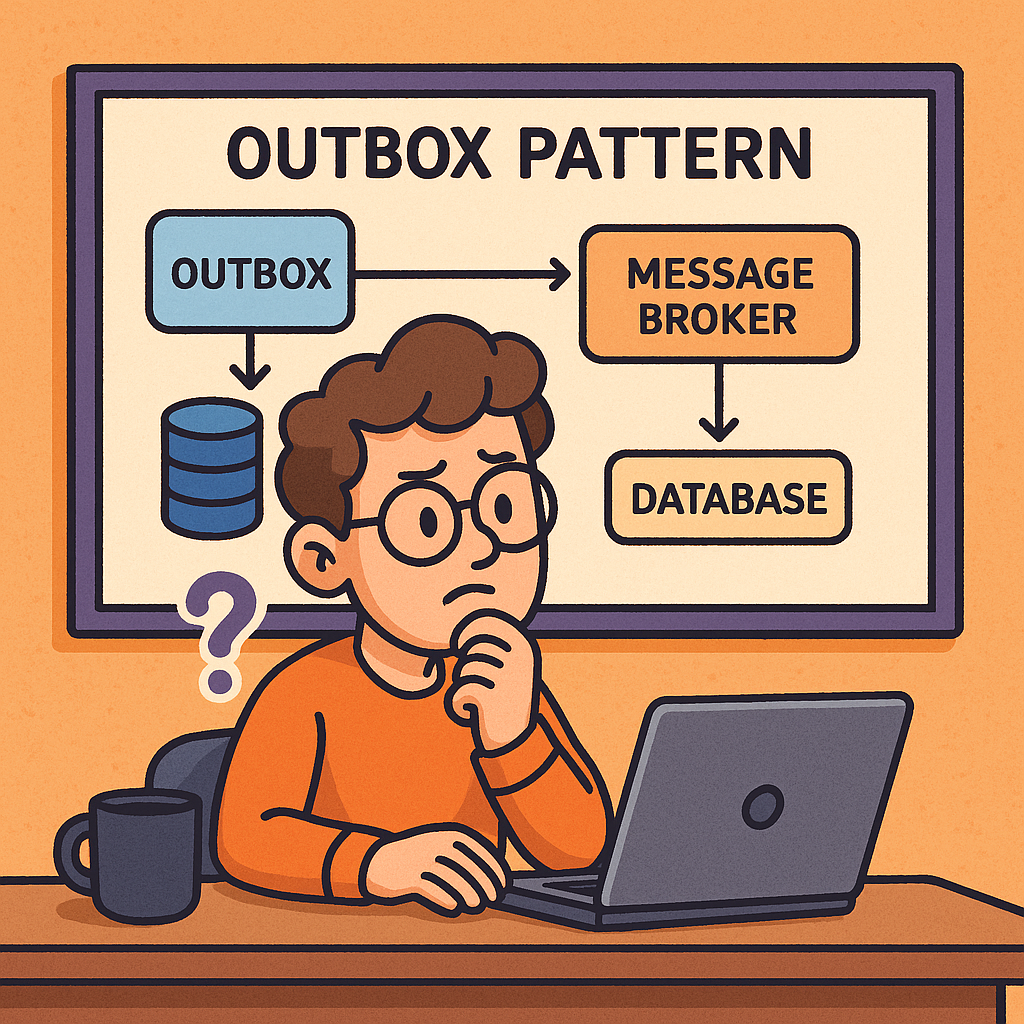
The Outbox Pattern is a design pattern commonly used in distributed systems and microservices to ensure reliable message delivery. It addresses the problem of data consistency when a…
Pair programming is a software development technique where two programmers work together at one workstation. One developer, called the Driver, writes the code, while the other, the Observer…

PKCE (Proof Key for Code Exchange) is a security extension to OAuth 2.0 that protects the Authorization Code flow from interception attacks—especially for public clients like mobile apps,…
Polyglot interop (polyglot interoperability) refers to the ability of different programming languages to work together within the same system or application. Instead of being confined to a single…

A Deterministic Random Bit Generator (DRBG) is an algorithm that generates a sequence of random-looking bits from a given initial value called a seed. Unlike true random number…
Regression testing is a type of software testing that ensures recent code changes, bug fixes, or new features do not negatively impact the existing functionality of an application.…
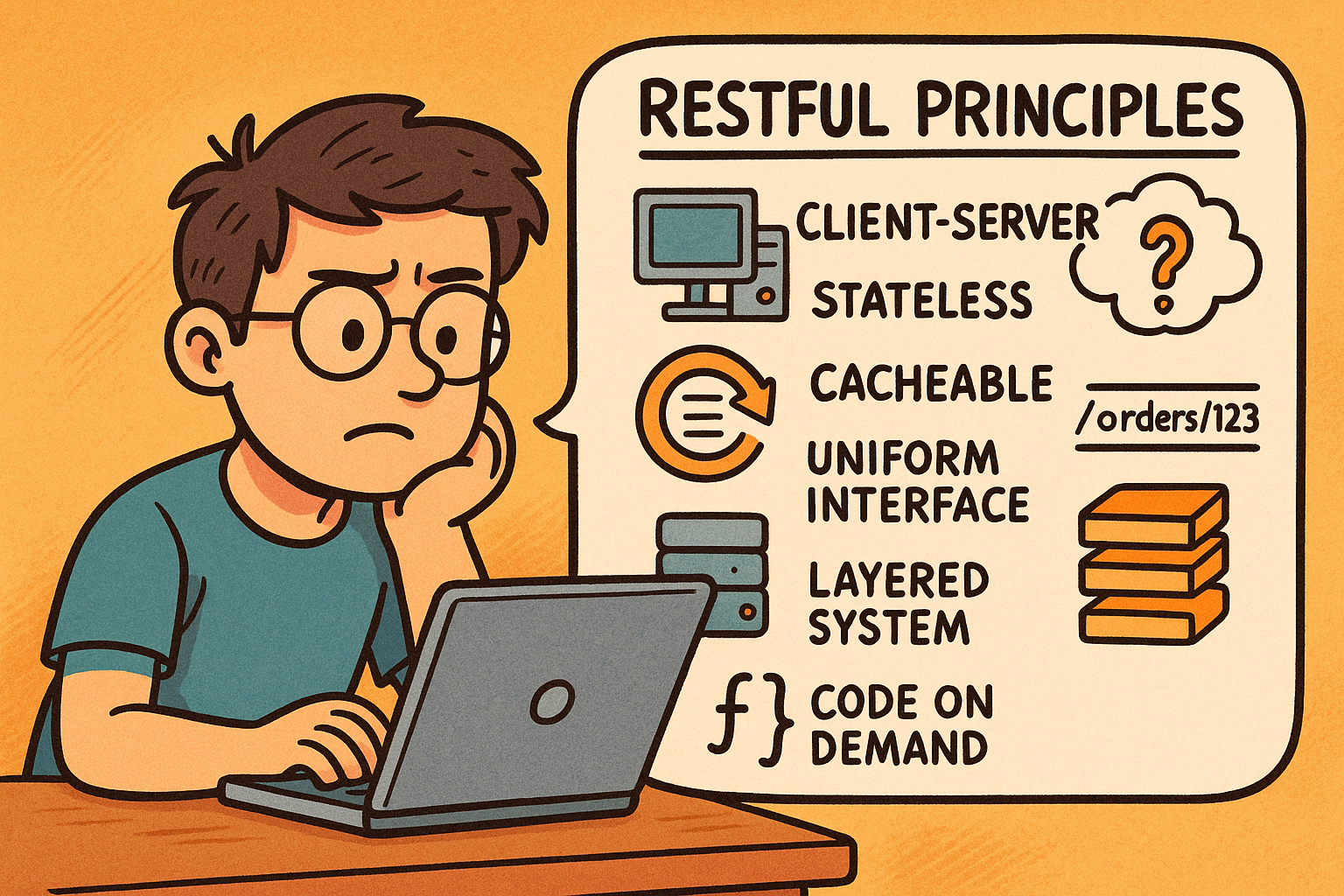
REST (Representational State Transfer) is an architectural style for designing networked applications. A RESTful API exposes resources (users, orders, posts, etc.) over HTTP using standard methods (GET, POST,…

Risk-Based Authentication (RBA) is an adaptive security approach that evaluates the risk level of a login attempt and adjusts the authentication requirements accordingly. Instead of always requiring the…
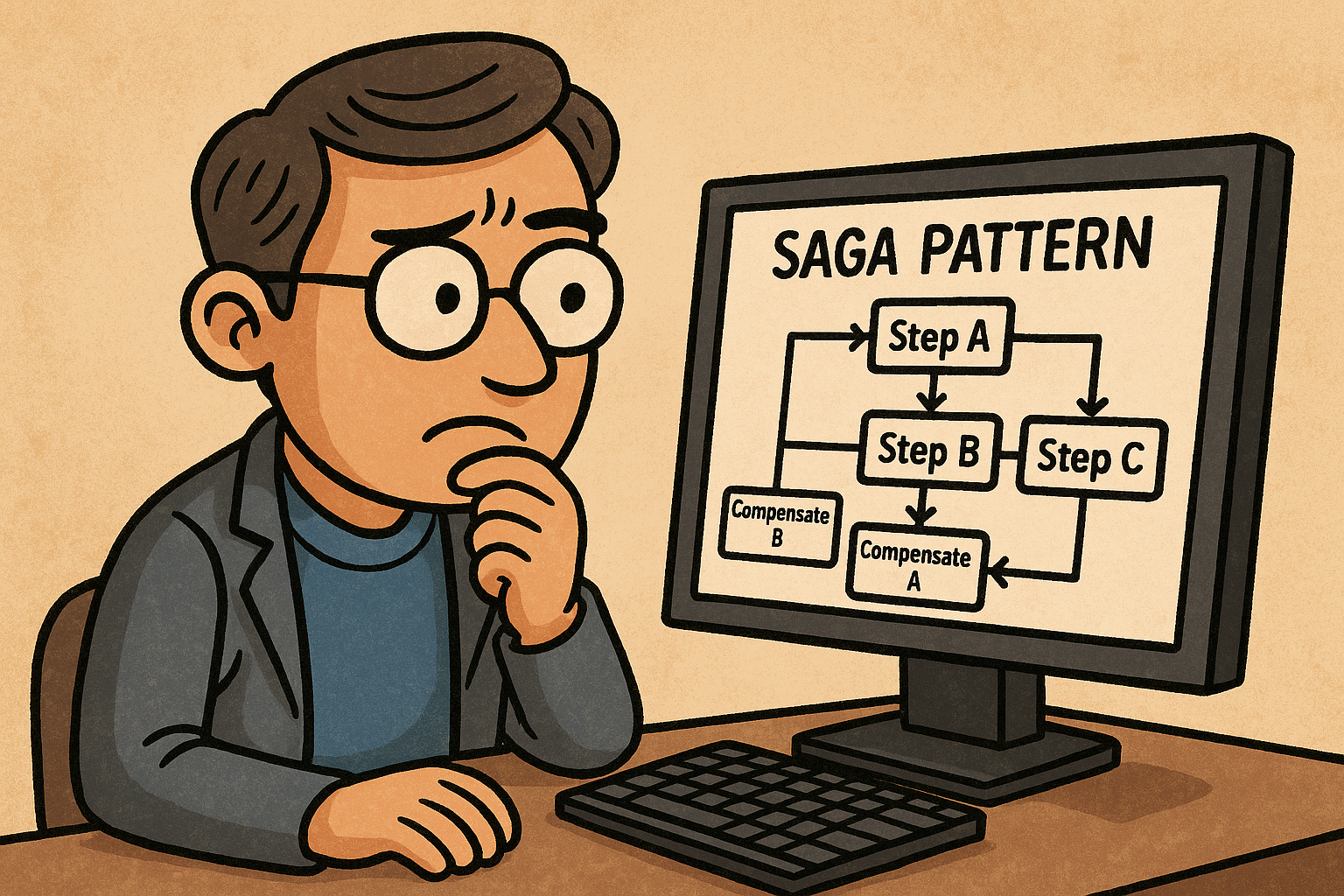
A saga is a sequence of local transactions that update multiple services without a global ACID transaction. Each local step commits in its own database and publishes an…
Salted Challenge Response Authentication Mechanism (SCRAM) is a password-based authentication protocol standardized by the IETF (commonly used as a SASL mechanism).
In A/B testing, even the smallest imbalance in traffic allocation can lead to misleading results. This phenomenon is known as Sample Ratio Mismatch (SRM) — a hidden but…

Secure Socket Layer (SSL) is a cryptographic protocol originally designed to secure communication over networks. Modern “SSL” in practice means TLS (Transport Layer Security)—the standardized, more secure successor…
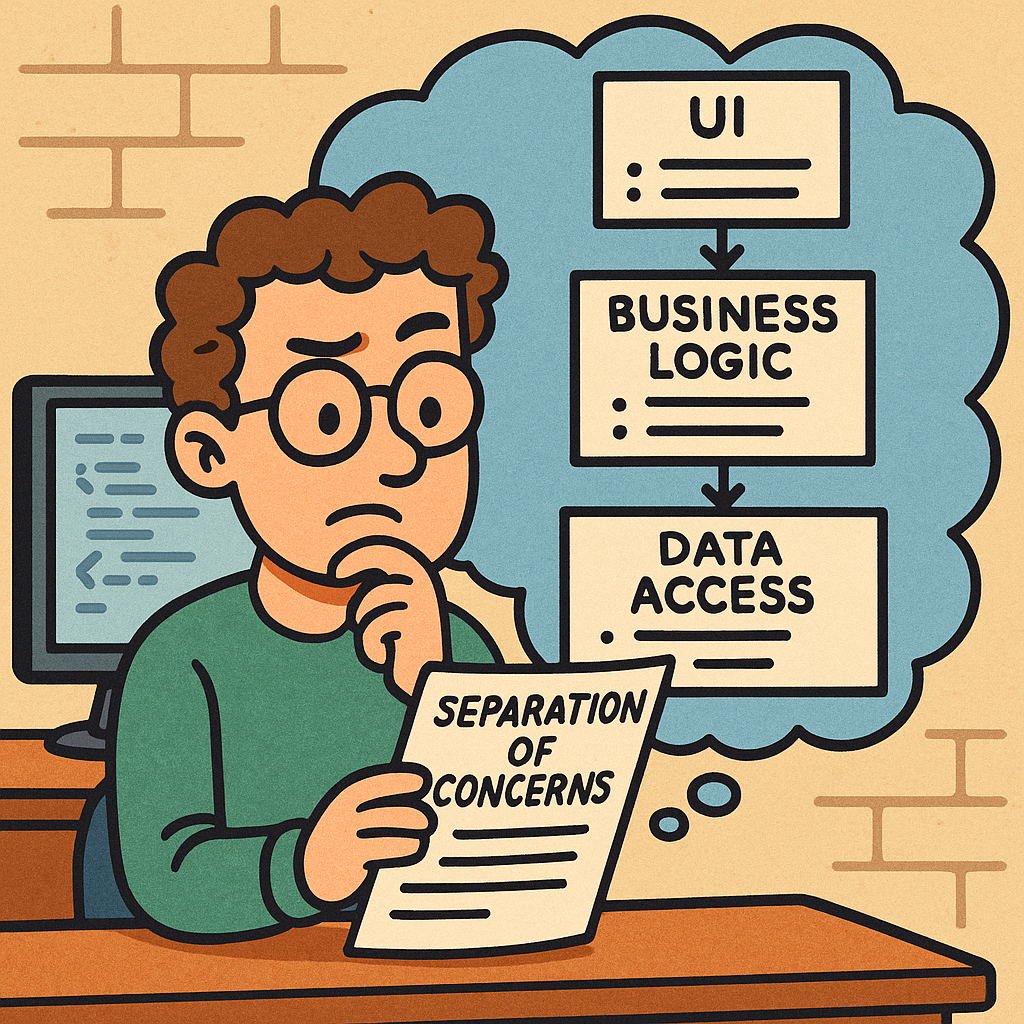
Separation of Concerns (SoC) is a foundational design principle: split your system into parts, where each part focuses on a single, well-defined responsibility. Done well, SoC makes code…

SASL is a protocol-agnostic authentication layer defined so that an application protocol (like IMAP or LDAP) can “hook in” standardized auth exchanges without reinventing them.
Single-Page Applications (SPAs) deliver app-like experiences on the web. This guide covers what SPAs are, how they work, their history, benefits and challenges, real-world examples, and step-by-step ways…

Smoke Testing (also called Build Verification Testing) is a type of software testing that ensures the most important functions of an application work correctly after a new build…
Stable bucketing is a crucial technique in A/B testing that ensures each user is consistently assigned to the same experimental group across multiple sessions or tests. By using…

A Standard Operating Procedure (SOP) is a versioned document that spells out the who, what, when, and how for a recurring task so it can be done consistently,…
State is the “memory” of a system—the data that captures what has happened so far and what things look like right now. State management is the set of…
System Testing is a type of software testing where the entire integrated system is tested as a whole. Unlike unit testing (which focuses on individual components) or integration…
Test Driven Development (TDD) is a software development practice where tests are written before the actual code. The main idea is simple: first, you write a failing test…
Tight coupling is when one component depends directly on the concrete implementation, lifecycle, and behavior of another. If A changes, B likely must change too. This is the…
Two-Phase Commit (2PC) is a distributed transaction protocol that ensures all participants in a transaction either commit or abort changes in a coordinated way. It is widely used…
An Application Binary Interface (ABI) defines the low-level, binary-level contract between two pieces of software — typically between a compiled program and the operating system, or between different…
An ArrayList is a resizable array implementation provided in many programming languages (for example, java.util.ArrayList in Java or List in C#). Unlike regular arrays that have a fixed…
Arrays are one of the most fundamental concepts in computer science and programming. Whether you are working with Java, Python, JavaScript, or PHP, arrays play a critical role…
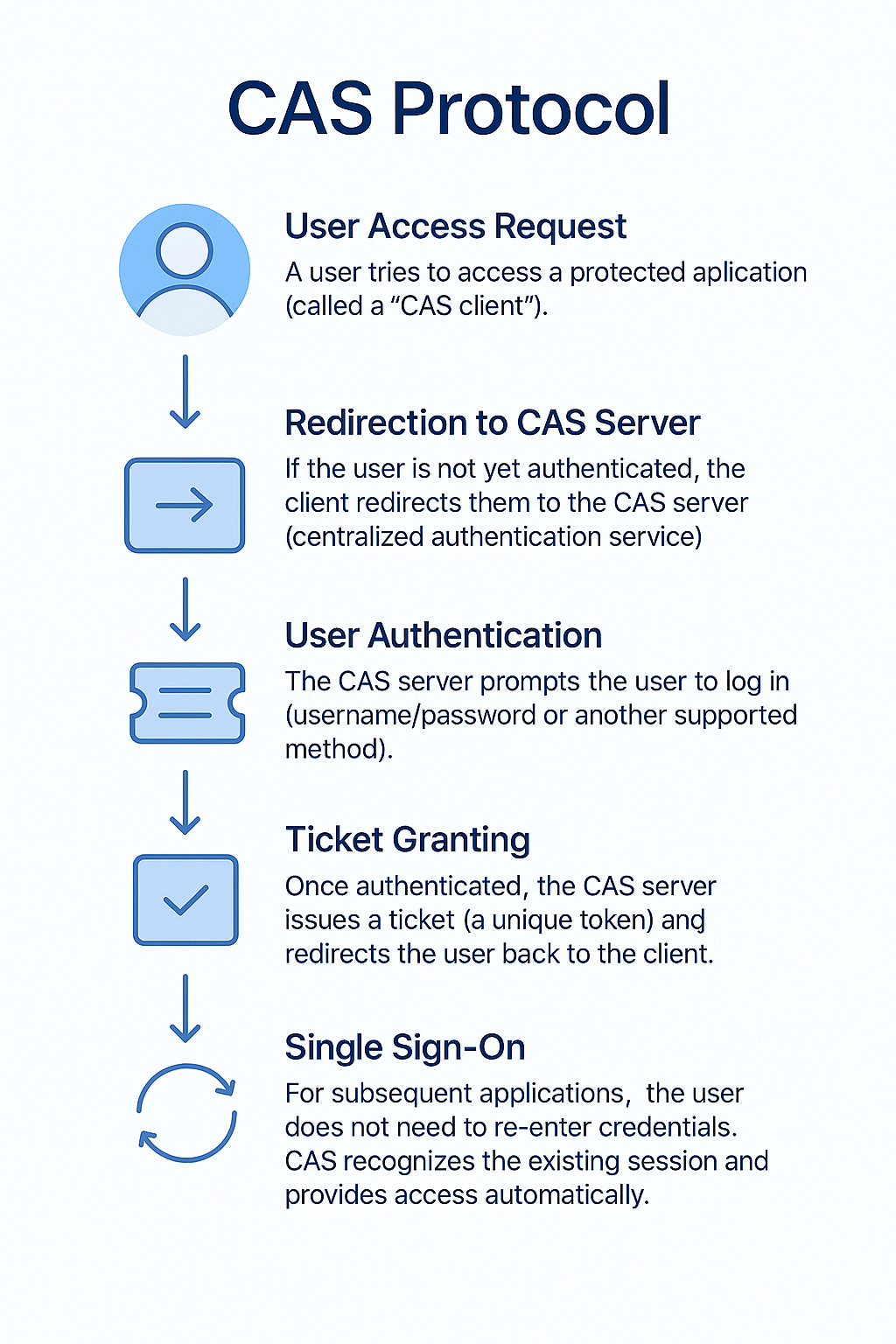
The Central Authentication Service (CAS) is an open-source, single sign-on (SSO) protocol that allows users to access multiple applications with just one set of login credentials. Instead of…
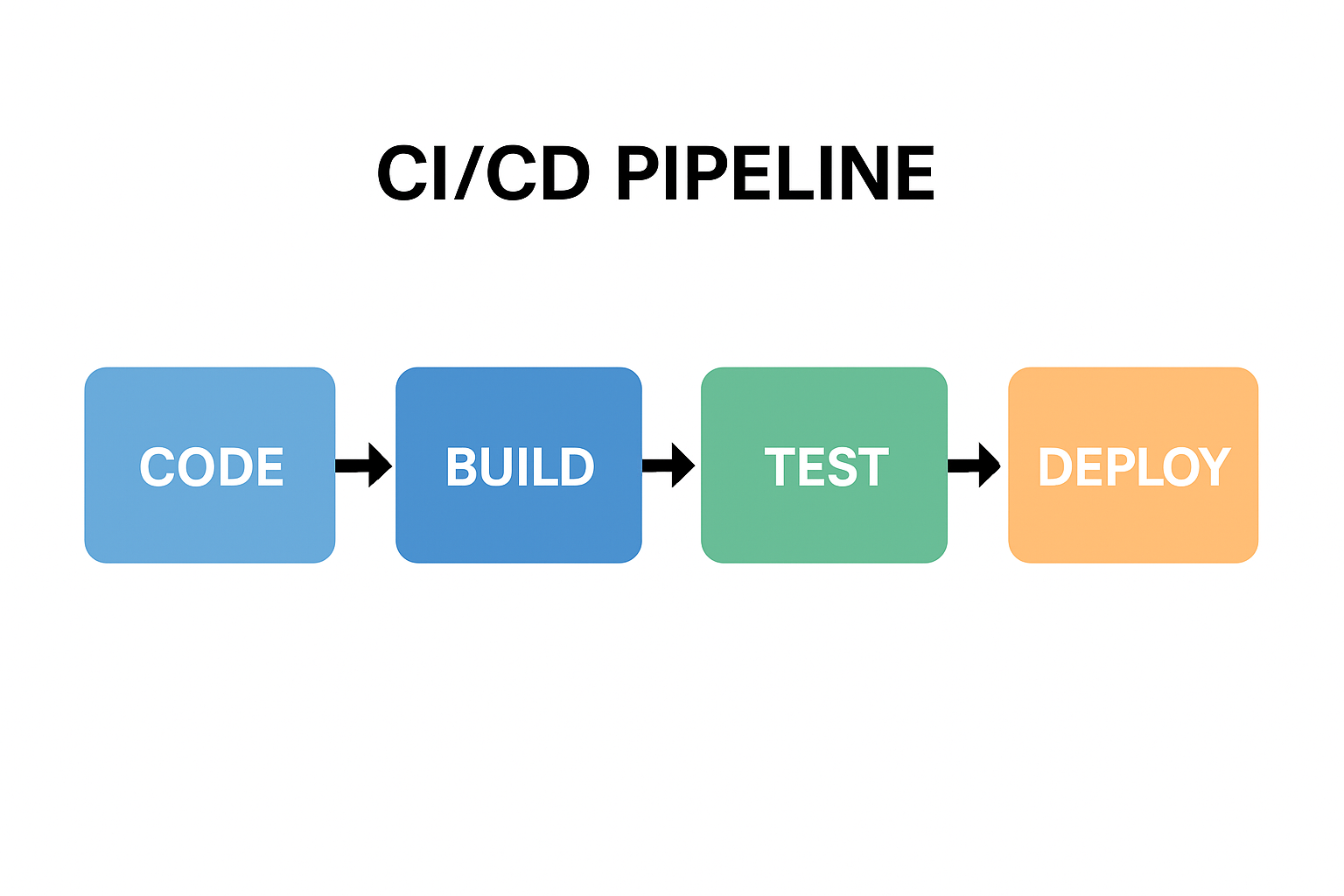
CI/CD stands for Continuous Integration and Continuous Delivery (or Deployment). A CI/CD pipeline is a series of automated steps that help developers build, test, and deploy software more…
Dependency Injection (DI) is a design pattern in software engineering where the dependencies of a class or module are provided from the outside, rather than being created internally.…
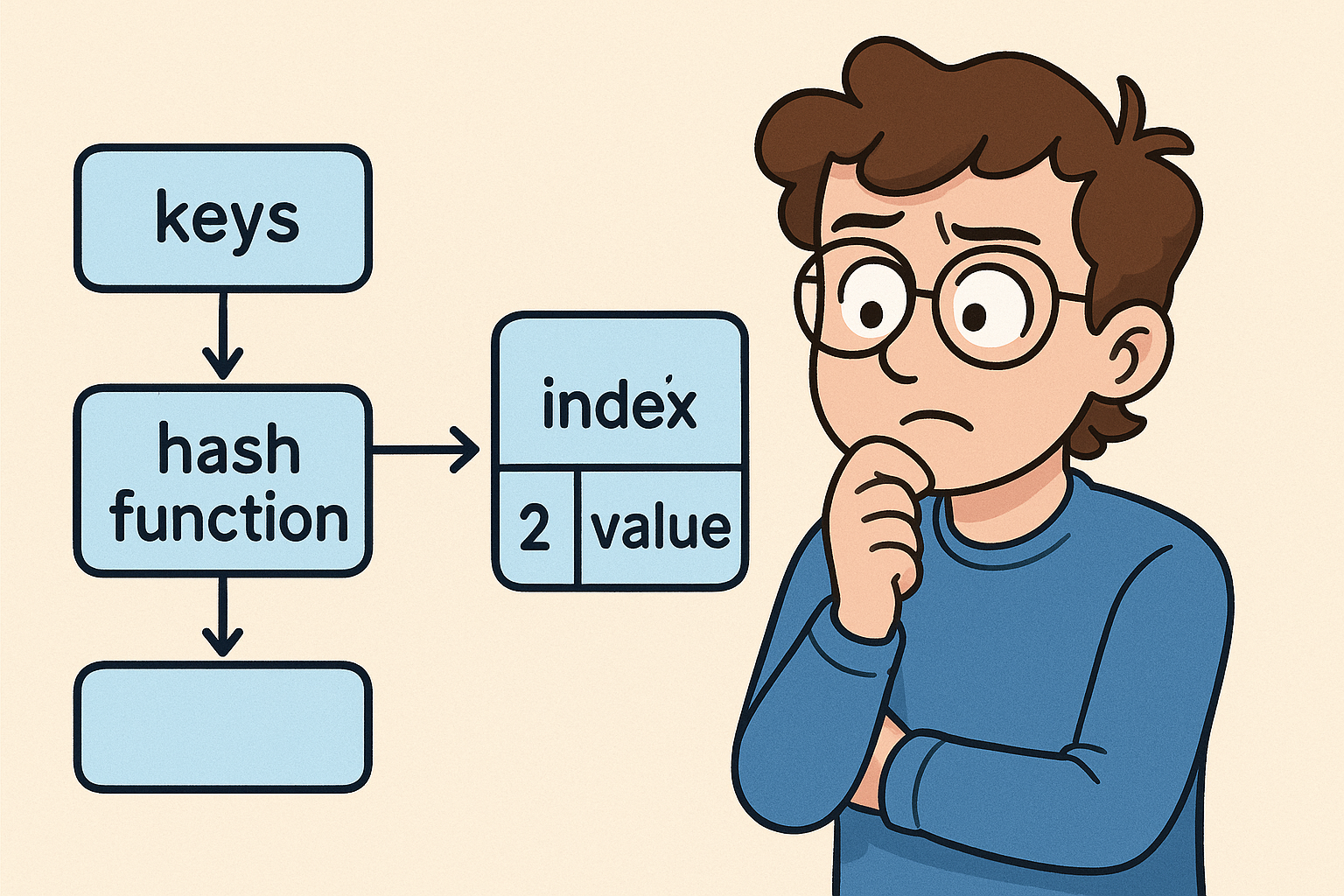
A hash table (also known as a hash map) is a data structure that stores key–value pairs. It uses a hash function to convert keys into indexes, which…

A Heisenbug is a type of software bug that seems to disappear or alter its behavior when you attempt to study, debug, or isolate it. In other words,…
In computer science, the term idempotent describes an operation that produces the same result even if it is executed multiple times. In other words, no matter how many…
A linked list is a linear data structure where elements (called nodes) are stored in separate memory locations and connected using pointers (links).
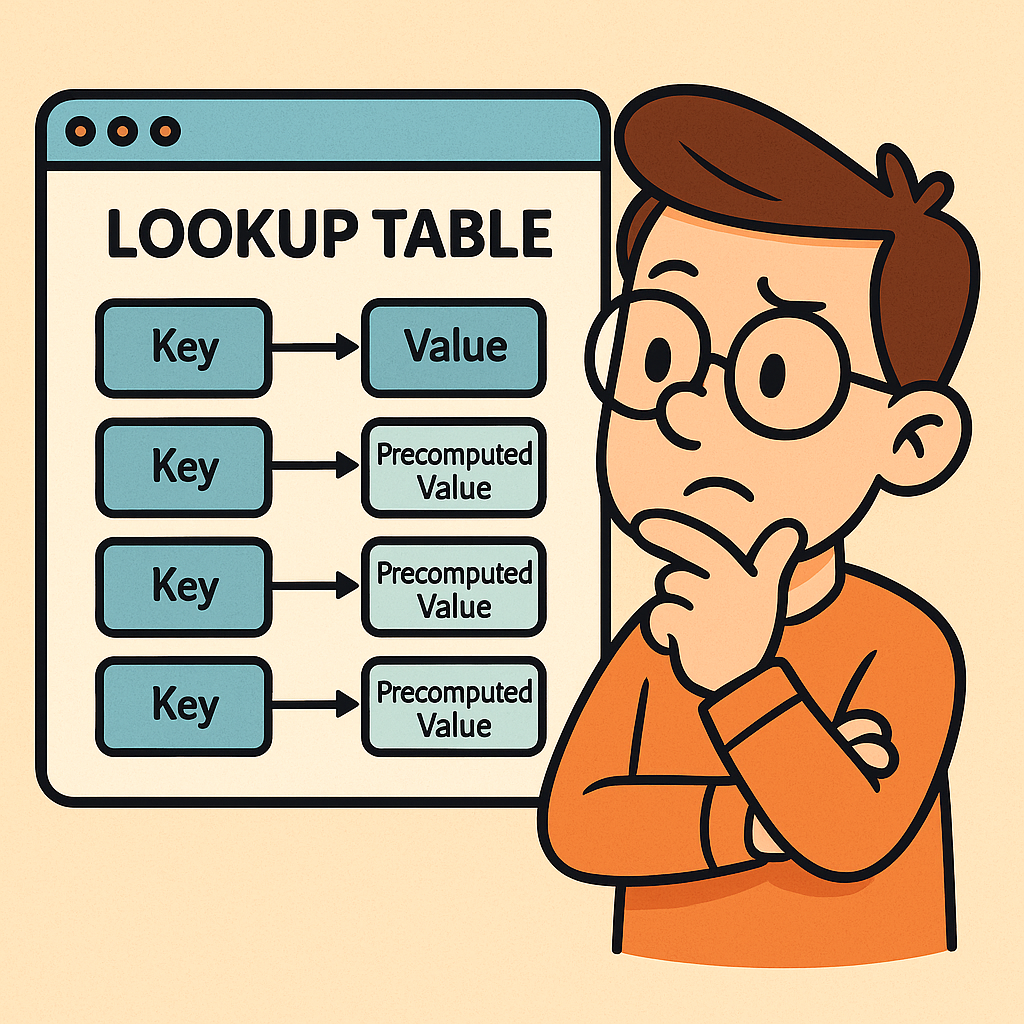
A lookup table (LUT) is a data structure, usually implemented as an array, hash map, or dictionary, that allows you to retrieve precomputed values based on an input…
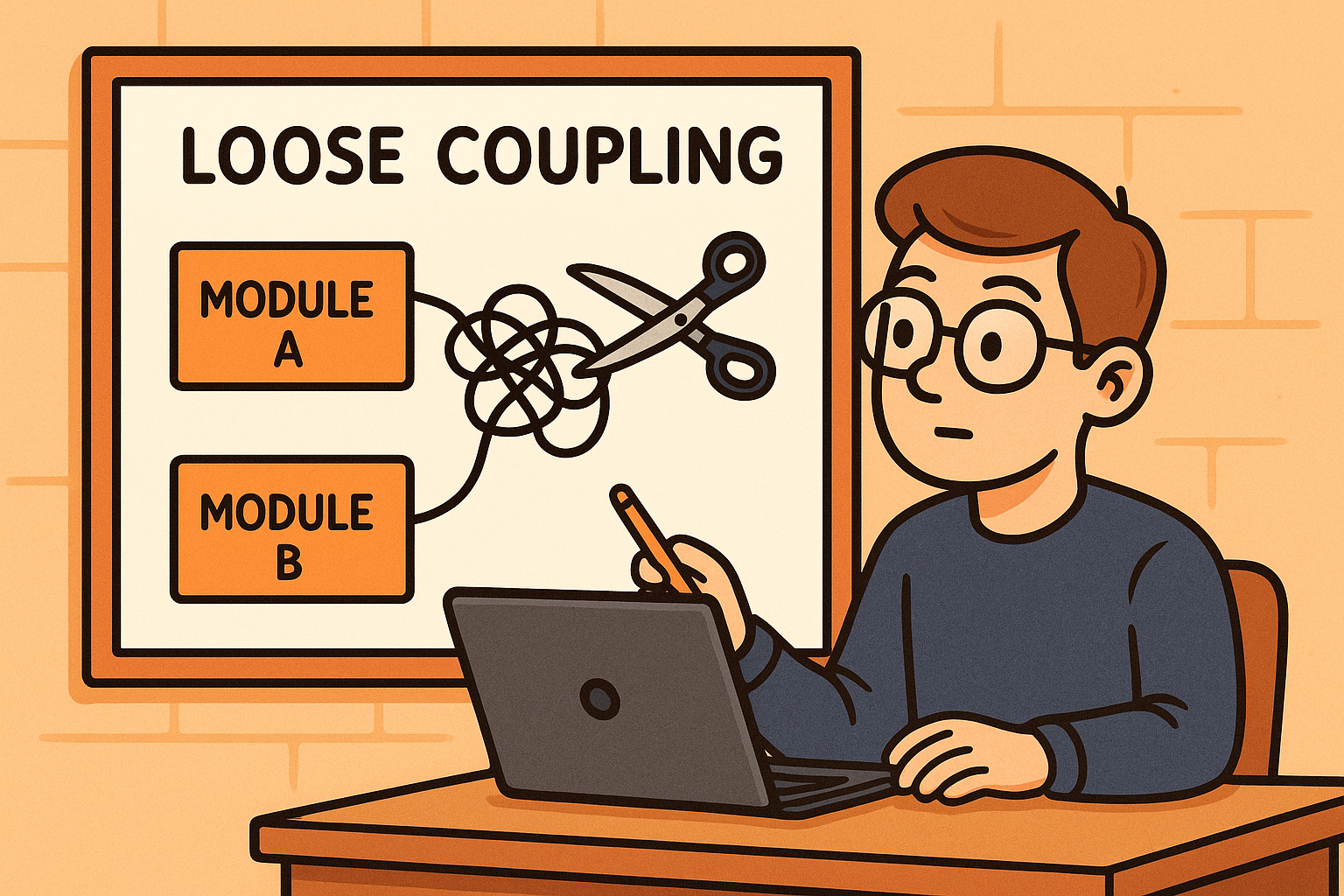
Loose coupling is a design principle in software engineering where different components, modules, or services in a system are designed to have minimal dependencies on one another. This…
Model Context Protocol (MCP) standardizes how LLMs safely access tools, data, and apps. This post explains MCP and MCP servers—their history, architecture, and security model—then shows practical benefits…
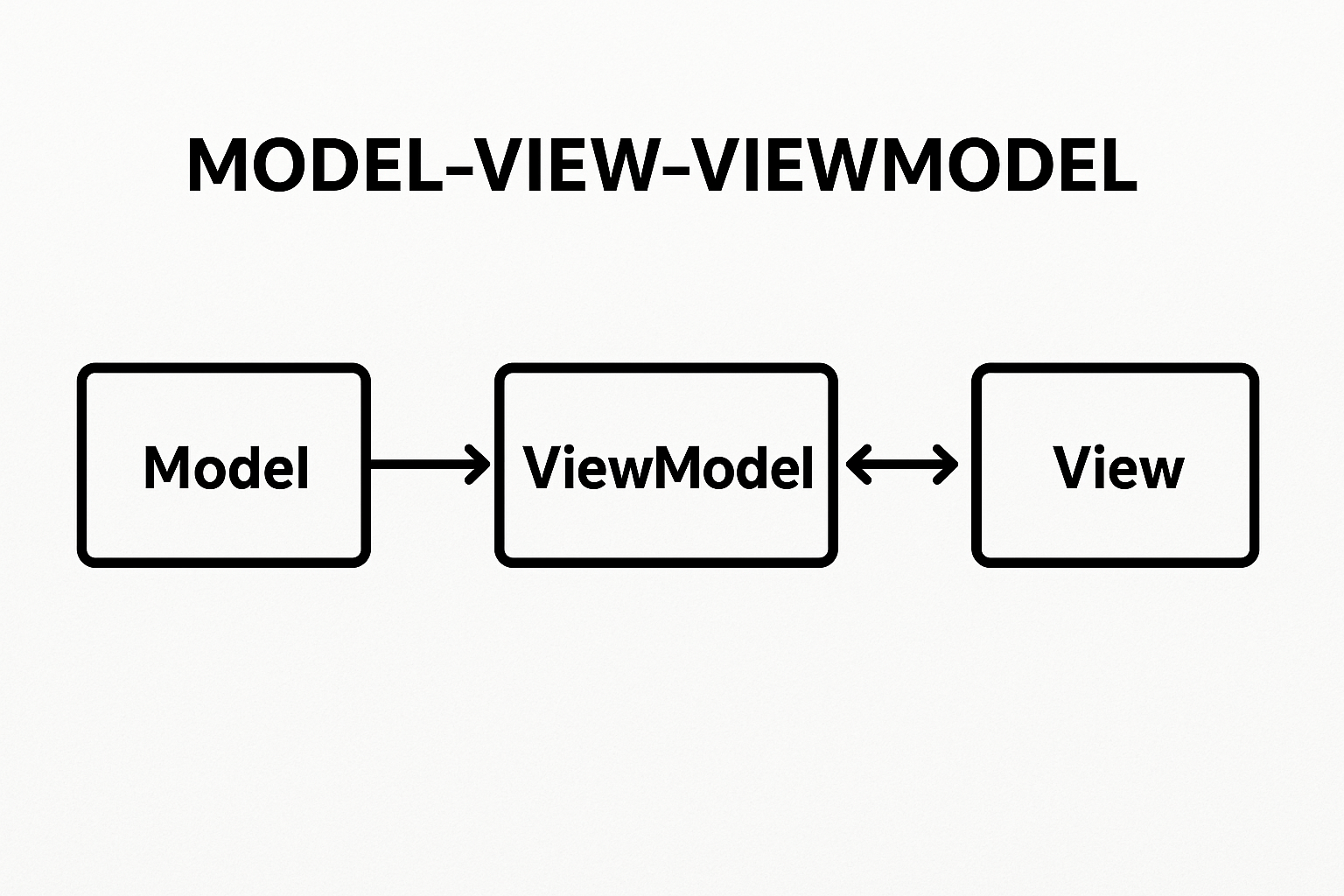
Model-View-ViewModel (MVVM) is a software architectural pattern that helps organize code by separating the user interface (UI) from the business logic. It acts as an evolution of the…
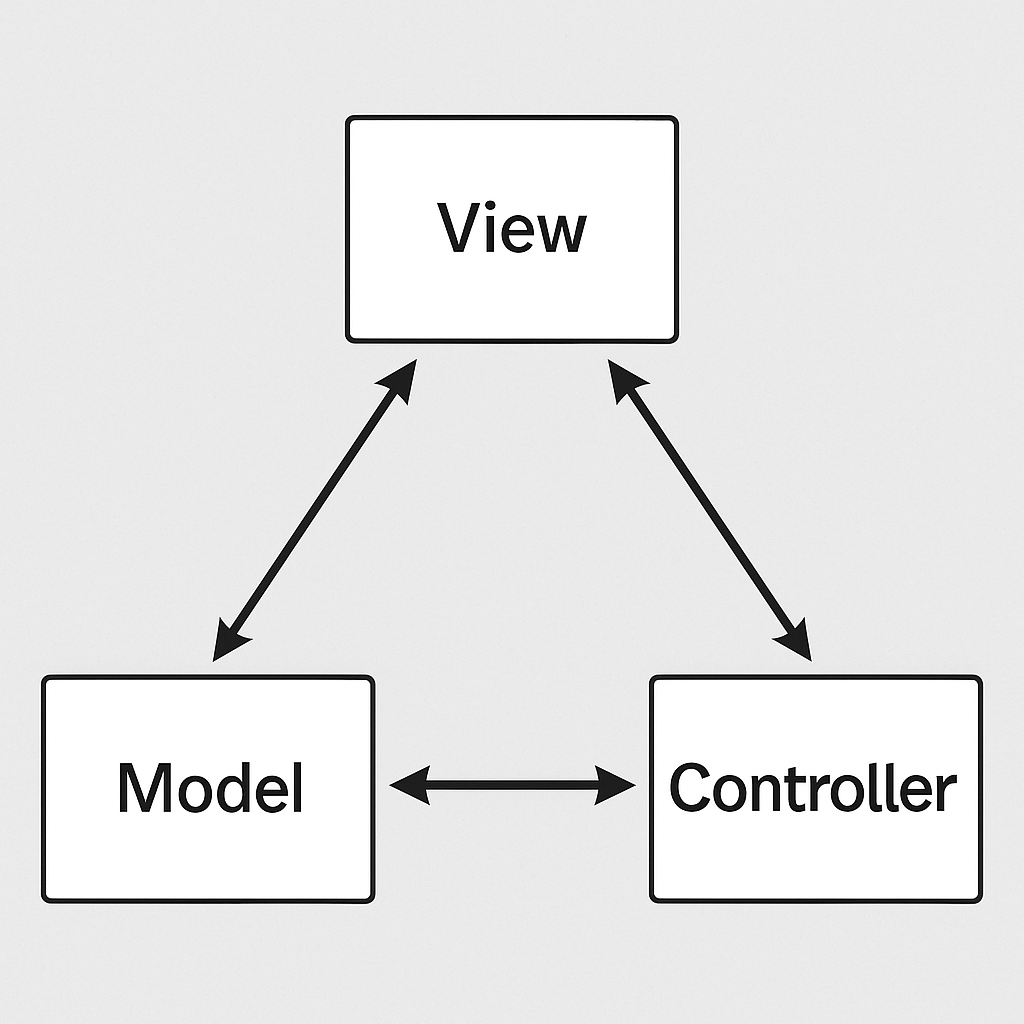
MVC stands for Model–View–Controller, a popular architectural pattern used in software engineering. An MVC framework provides a structured way to separate concerns in an application, making development, testing,…
OLTP stands for Online Transaction Processing. It refers to a type of database system designed to handle large numbers of small, quick operations such as insertions, updates, and…
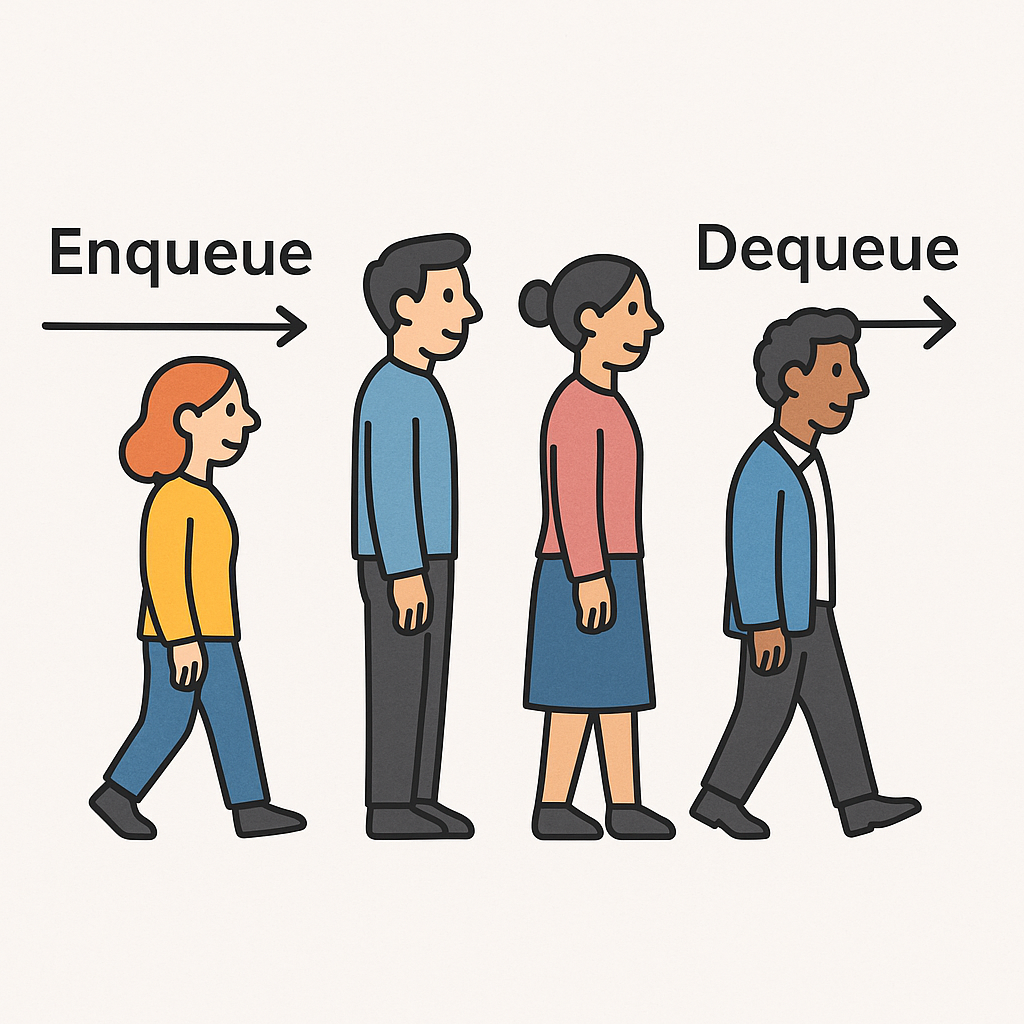
A queue is a fundamental data structure in computer science that follows the FIFO (First In, First Out) principle. This means the first element inserted into the queue…
When learning about data structures, one of the simplest yet most powerful concepts is the stack. Just like its real-world counterpart—a stack of plates in your kitchen—this structure…
CVE (Common Vulnerabilities and Exposures) is an international system that provides a standardized method of identifying and referencing publicly known cybersecurity vulnerabilities. Each vulnerability is assigned a unique…
In software engineering, one of the most valuable design principles is the DRY principle. DRY stands for “Don’t Repeat Yourself”, and it is a fundamental guideline that helps…
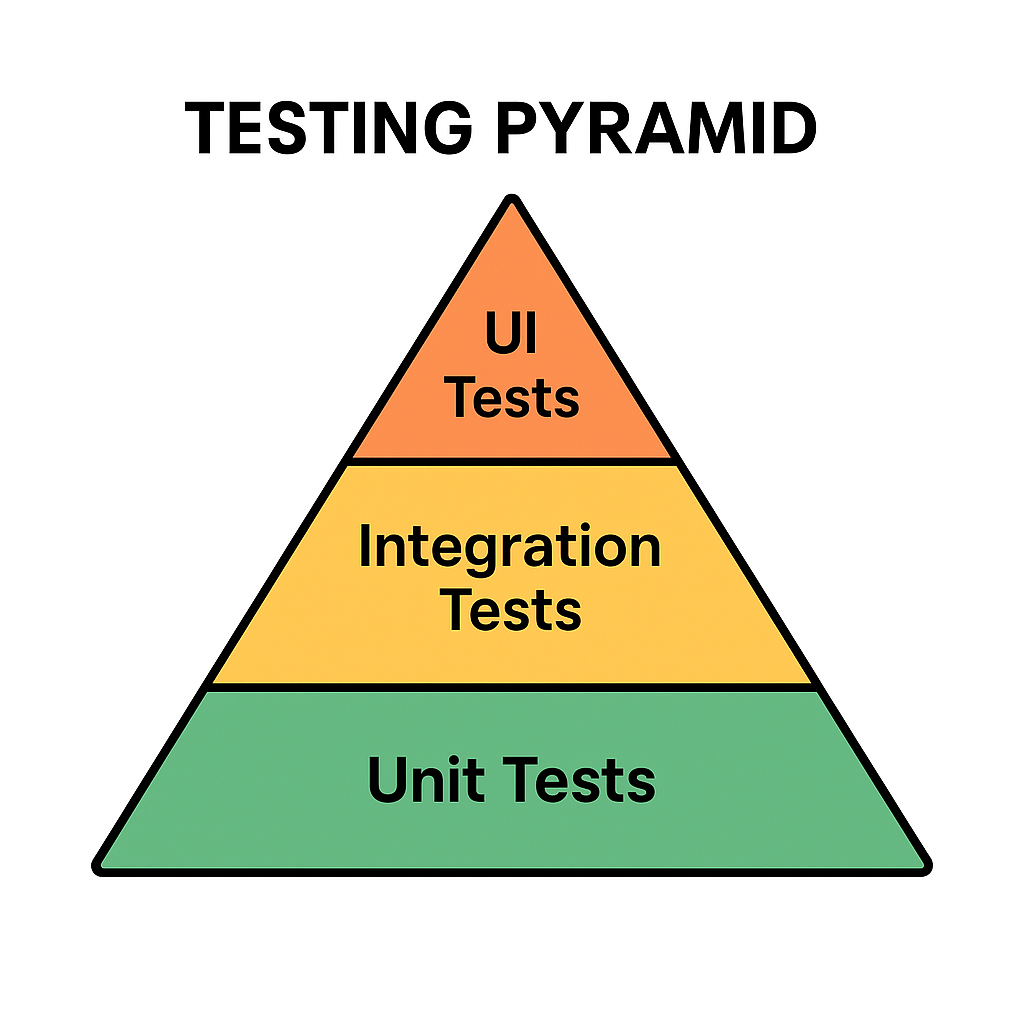
The Testing Pyramid is a concept introduced by Mike Cohn in his book Succeeding with Agile (2009). It illustrates the ideal distribution of automated tests across different levels…
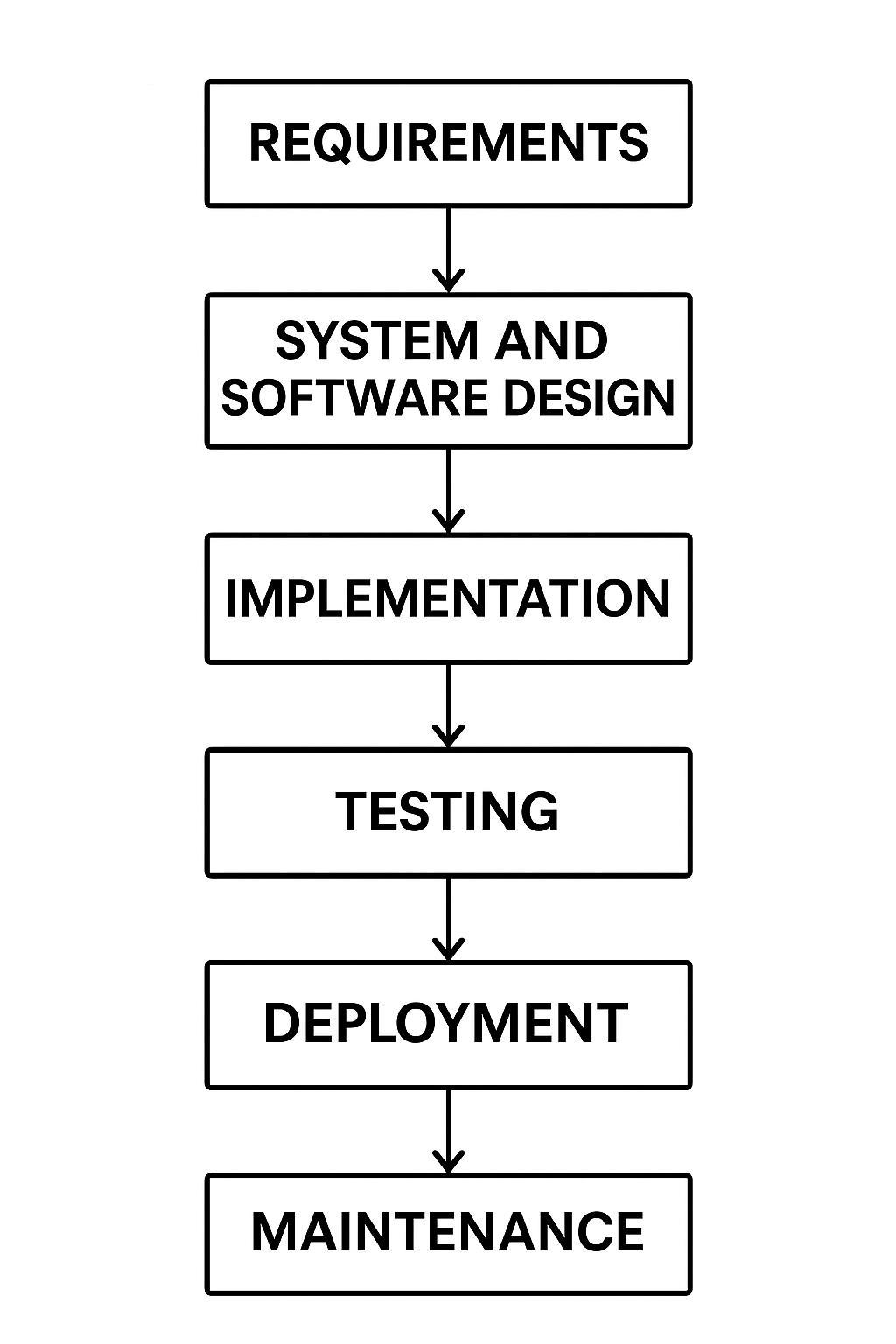
The Waterfall Model is one of the earliest and most traditional approaches to software development. It follows a linear and sequential design process, where each phase must be…
YAGNI stands for “You Aren’t Gonna Need It”. It is a principle from Extreme Programming (XP) that reminds developers not to implement functionality until it is absolutely necessary.…

When we study algorithms, we often come across notations like Big O, Omega, and Theta. Among these, Theta (Θ) plays a special role because it gives us a…
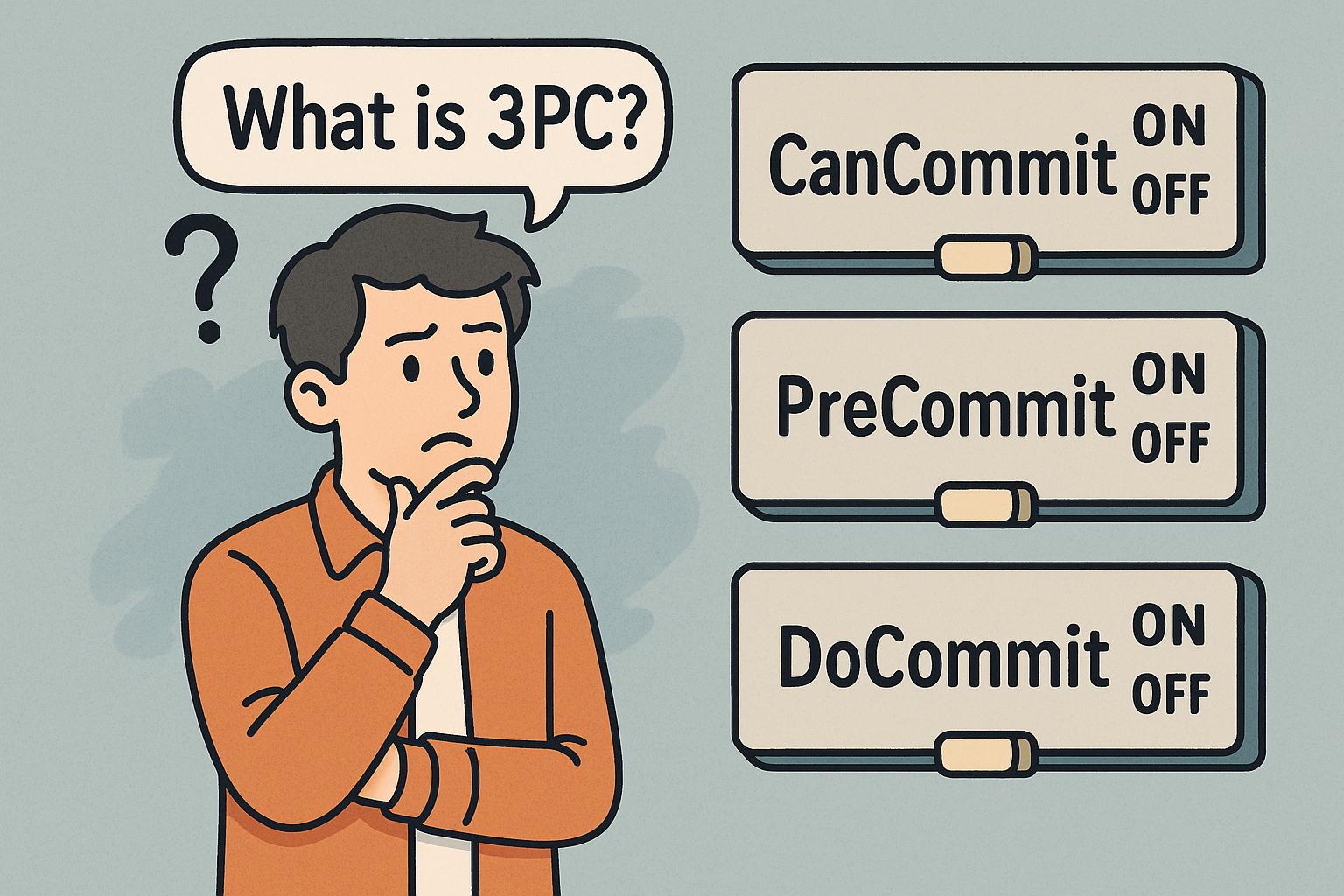
Three-Phase Commit (3PC) is a distributed consensus protocol used to ensure that a transaction across multiple nodes in a distributed system is either committed by all participants or…

Transport Layer Security (TLS) is a cryptographic protocol that ensures secure communication between computers over a network. It is the successor to Secure Sockets Layer (SSL) and is…
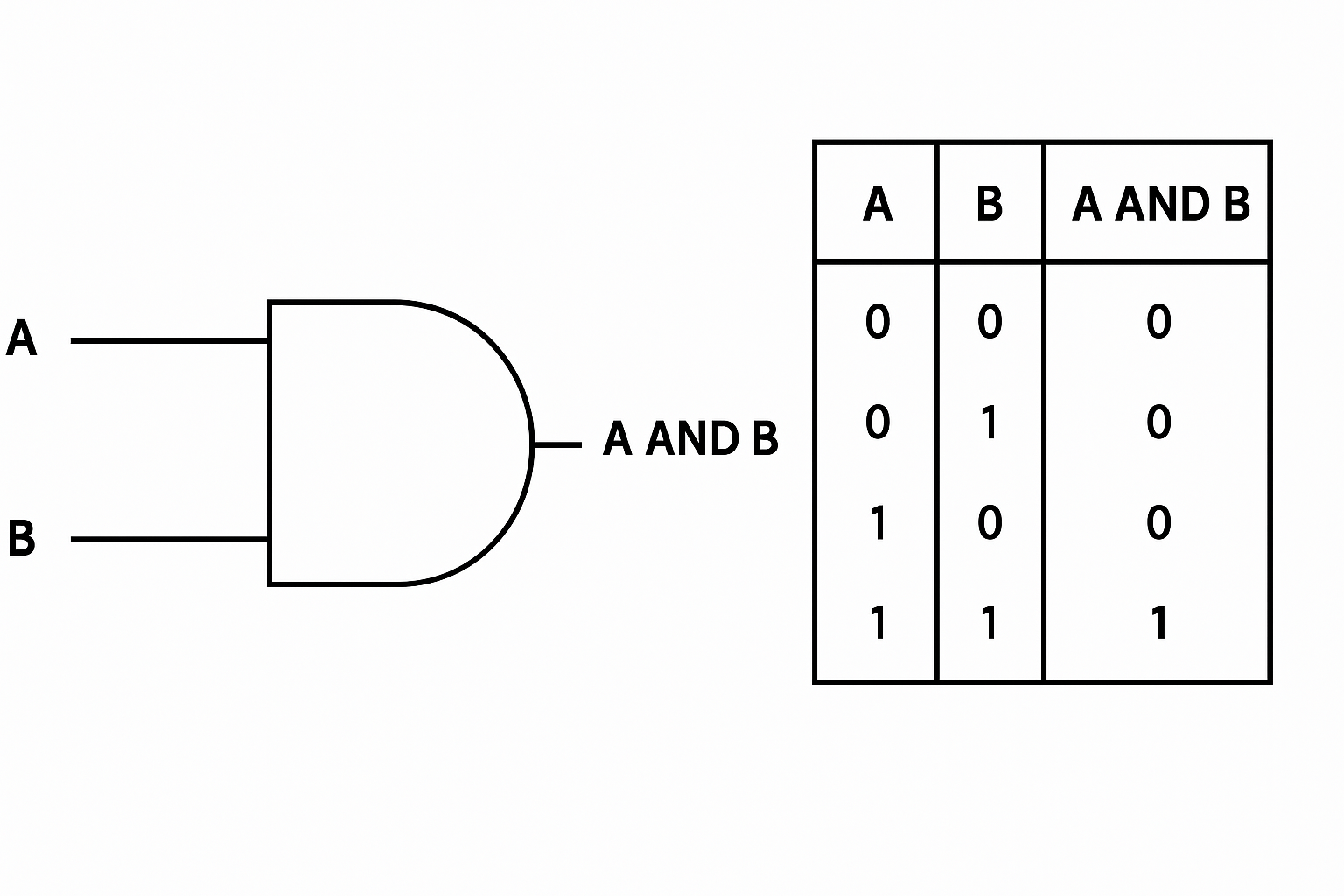
A truth table is a tabular representation of all possible values of logical variables and the results of applying logical operations to them. Each row of the table…
In A/B testing, the unit of randomization defines what exactly gets assigned to each experimental variant — a user, a device, a session, or even an entire store.…
A practical, end-to-end guide to unit testing—history, core concepts, when to write tests, benefits, and a step-by-step plan to integrate unit tests into your current software development process.

A Man-in-the-Middle (MITM) attack is when a third party secretly intercepts, reads, and possibly alters the communication between two parties who believe they are talking directly to each…
A modular monolith is a software architecture style where an application is built as a single deployable unit (like a traditional monolith), but internally it is organized into…
CAPTCHA, short for Completely Automated Public Turing test to tell Computers and Humans Apart, is one of the most common tools used to protect websites from bots and…
Ω (Omega) provides a lower bound on algorithm complexity. It tells us the minimum resources (time, comparisons, operations) an algorithm will always need as the input grows.